Keynote and Invited Talks
Keynote Talk Speakers
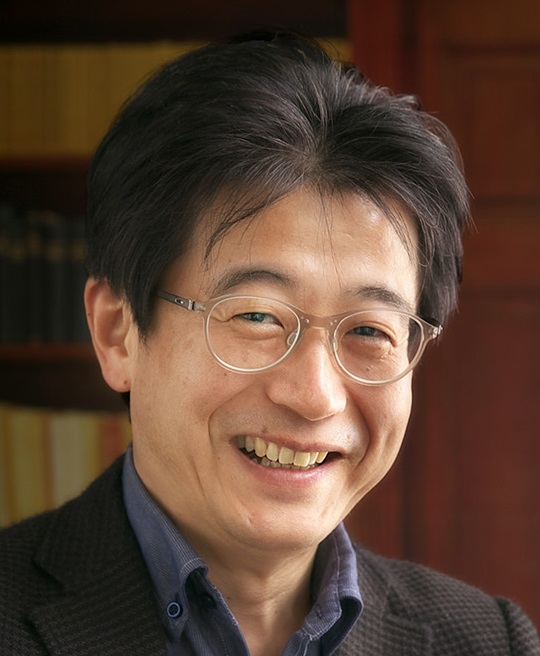 Prof. Tsuyoshi Takagi
Prof. Tsuyoshi Takagi
Professor at Mathematical Cryptography Laboratory in The University of Tokyo
Keynote Talk I: Recent Developments in Post-Quantum Cryptography
Abstract
The security of current public-key cryptosystems relies on the hardness of factoring large integers or solving discrete logarithm problems. However, these computational problems can be solved in polynomial time using a quantum computer. This vulnerability has prompted research into post-quantum cryptography using alternative mathematical problems that are secure in the era of quantum computers.
In this talk, we give an overview of recent developments in post-quantum cryptography. In 2016, the National Institute of Standards and Technology (NIST) began the standardization project of post-quantum cryptography. Very recently, NIST has selected CRYSTALS-Kyber for public-key encryption and key-establishment, and CRYSTALS-Dilithium, FALCON, SPHINCS+ for digital signature algorithms, where CRYSTALS-Kyber, -Dilithium, and FALCON are lattice-based cryptosystems and SPHINCS+ is a hash-based signature. In this talk, we explain the state-of-the-art of security evaluation in lattice-based cryptosystems.
 Prof. Hervé Debar
Prof. Hervé Debar
Professor and Dean of Telecom SudParis
Keynote Talk II: Vulnerability assessment in complex distributed software systems
Abstract
Vulnerability assessment has become a critical aspect for protecting information system from attacks and prioritizing actions. Vulnerability information is constituted of multiple sources and is often a mix of automated and manual generation. In this presentation, we address the issue of assessing the vulnerability state of critical infrastructures, in our case the healthcare ecosystem. While information about vulnerabilities has made a lot of progress in recent years, it remains difficult to integrate in distributed environments, with multiple interacting entities. The content of vulnerability information also requires additional automated processing methods to increase quality and facilitate reuse. In this presentation, I will present the HEIR architecture and a method to compute a vulnerability score for a given environment, and enable comparison of scores between multiple environments of a similar nature. Since this method requires obtaining a score for each vulnerability as input, I will present a model of vulnerability information that shows the connections between multiple information sources. Since most of the information is in textual form, I will conclude with a description of a technique based on Natural Language Processing to obtain the required quantification information from this textual descriptions.
Invited Talk Speakers
 Dr. Abdul Rahman Taleb
Dr. Abdul Rahman Taleb
PhD researcher at CryptoExperts company and LIP6 laboratory in Paris,
Sorbonne University, France.
Invited Talk I: Random Probing Security: Towards Bridging the Gap Between Theory and Practice
Abstract
Side-channel attacks exploit the physical leakage of a device executing cryptographic implementations to extract the manipulated secrets. They can be built from cheap equipment and can generally recover the keys in a limited time without specific protections. Since discovering these attacks in the late nineties, the community has investigated several approaches to counteract them. Among these approaches, masking is one of the most deployed in practice. The main idea of masking is to split the information between several variables called shares. An attacker must collect and aggregate the information from all these variables to recover sensitive data, which becomes exponentially hard with the number of shares as each observation comes with noise.
The community then introduced the concept of leakage models to theoretically reason on the security of such masked implementations. So far, the most widely used leakage model is the probing model defined by Ishai, Sahai, and Wagner (CRYPTO 2003), where we model the leakage as the exact values of t intermediate variables chosen by the attacker. While it is advantageous for security proofs, it does not capture an adversary exploiting full leakage traces, e.g., in horizontal attacks. Those attacks target the multiple manipulations of the same share to reduce noise and recover the corresponding value. Therefore, the community is focusing on more realistic leakage models, such as the random probing model. The leakage is assumed to gather the exact value carried out by each circuit wire with a probability of p. The security tightly reduces to the security in the noisy leakage model in which each variable leaks a noisy function of its value. The noisy leakage model is the closest to the reality of physical leakage but is less convenient for security proofs. The random probing model can also be extended to capture glitches or other side effects.
During this talk, I will briefly present the relations between the different leakage models, then present our recent works on providing constructions and security proofs in the random probing model. These works are a step forward in bridging the gap between the practical security of masked implementations and the theoretically proven security of their constructions.
 Dr. Takuya Watanabe
Dr. Takuya Watanabe
A researcher at NTT Social Informatics Laboratories, Japan.
Invited Talk II: Attacking the Web to Defend the Web
Abstract
Offensive analysis of computer systems is a promising way to identify and remediate vulnerabilities before attackers exploit them. In particular, since the majority of web services in the wild are running in a black box, we need to explore their security flaws with a well-designed strategic approach. In this talk, I will show two types of web attack concepts that we have discovered and present what we have learned from the process of identifying and countering them. Our attacks combine the exploitation of common features of web applications with informatics observations. Therefore, our attacks are undetectable by existing tools and affect a large number of web services. More specifically, we have demonstrated procedures that allow for persistent man-in-the-middle attacks or de-anonymization against web users. While these findings are helpful in designing secure web applications, an adequate vulnerability disclosure model must be developed to prevent harmful impacts on stakeholders. Our efforts have led services and browsers to adopt measures such as new control mechanisms for cookies and domain name isolation. I will also discuss collaboration across organizations to mitigate attacks and future directions for continuous and productive offensive security research.

We will have keynote talks from the following world-leading researchers. (To be updated)