[
MWS2008 |
MWS2009 |
MWS2010 |
MWS2011 |
MWS2012 |
MWS2013 |
MWS2014
]
MWS 2015
October 21 (Wed) - 23 (Fri), 2015
Nagasaki Brick Hall, Nagasaki, Japan
Nagasaki Shimbun Culture Hall, Nagasaki, Japan
Photo story of MWS 2015
 |
Nagasaki Brick Hall |
 |
Nagasaki Shimbun Culture Hall |
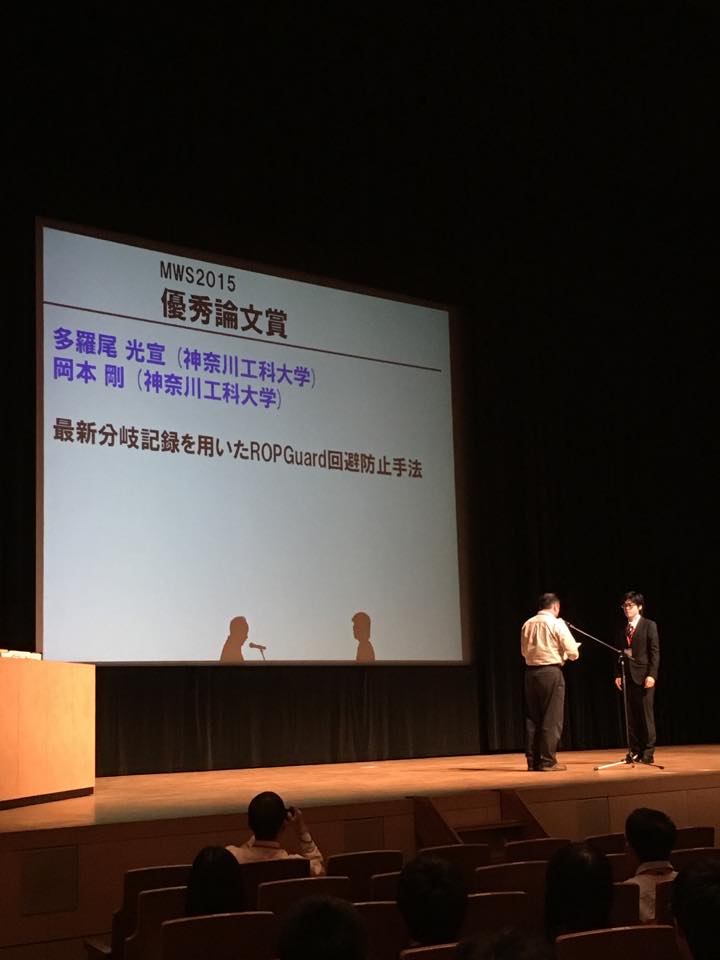
Award Ceremony
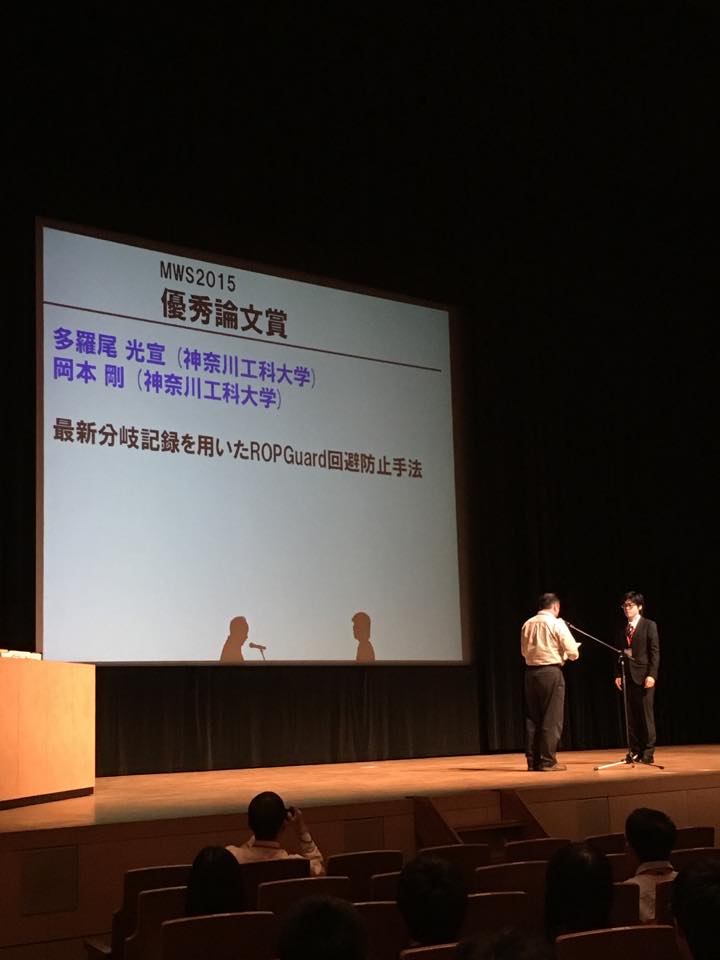 |
MWS2015 Best Paper Award:
ROPGuard Bypass Prevention Method using Last Branch Recording Facilities,
Mitsunobu Tarao (Kanagawa Institute of Technology)
and
Takeshi Okamoto (Kanagawa Institute of Technology). |
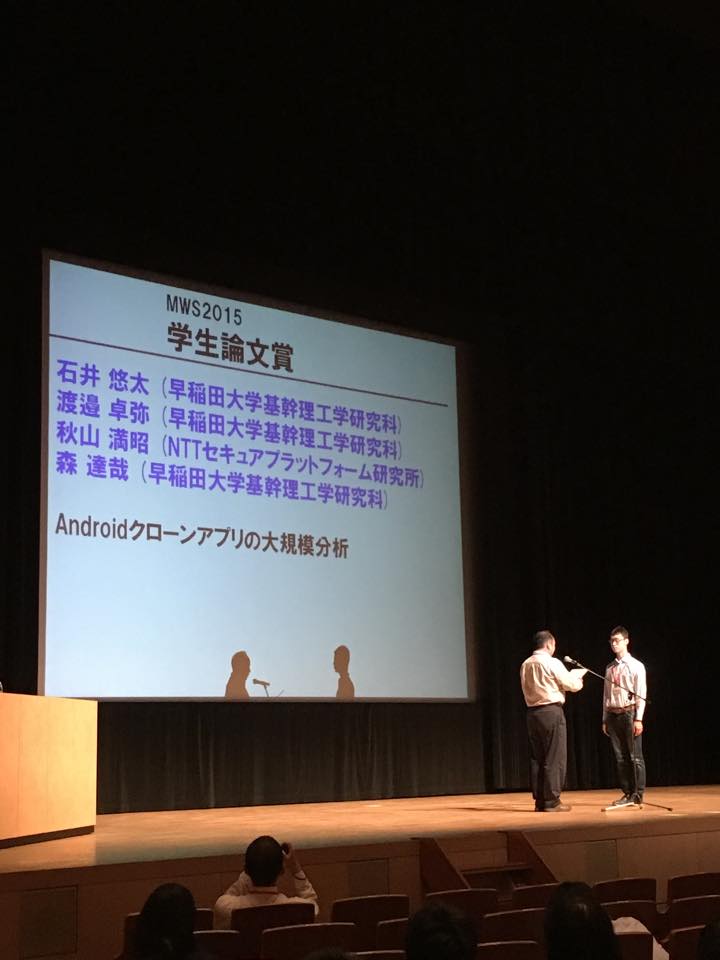 |
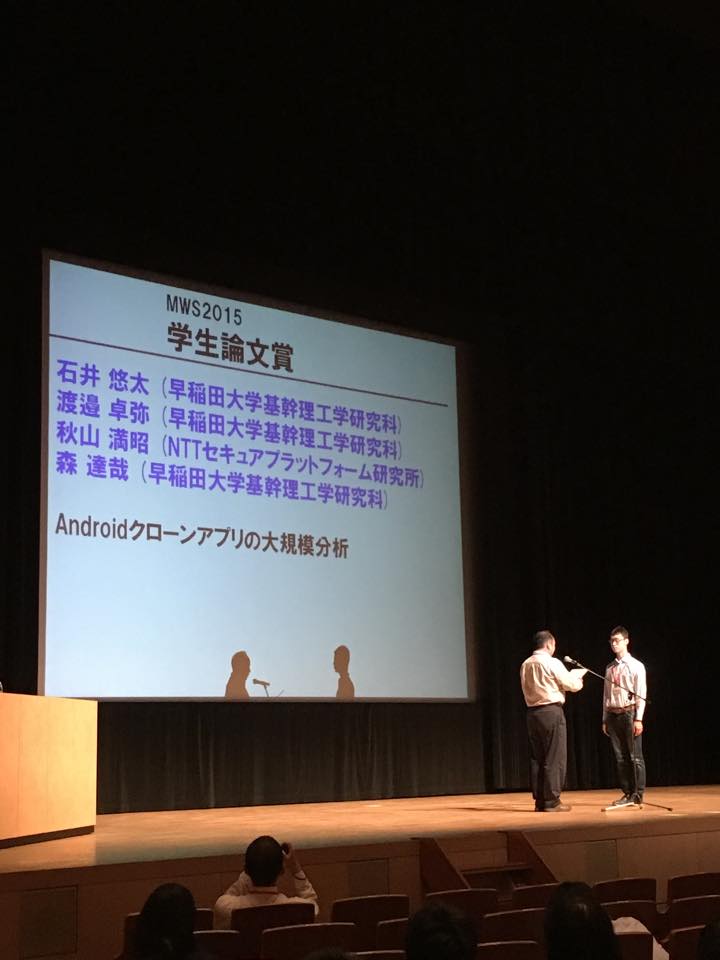
MWS2015 Best Student Paper Award:
A Large-scale Analysis of Cloned Android Apps,
Yuta Ishii (Waseda University),
Takuya Watanabe (Waseda University),
Mitsuaki Akiyama (NTT Secure Platform Laboratories)
and
Tatsuya Mori (Waseda University). |
|
|
Team Name |
Total Score (Rank) |
Technical Score (Rank) |
Presentation Score (Rank) |
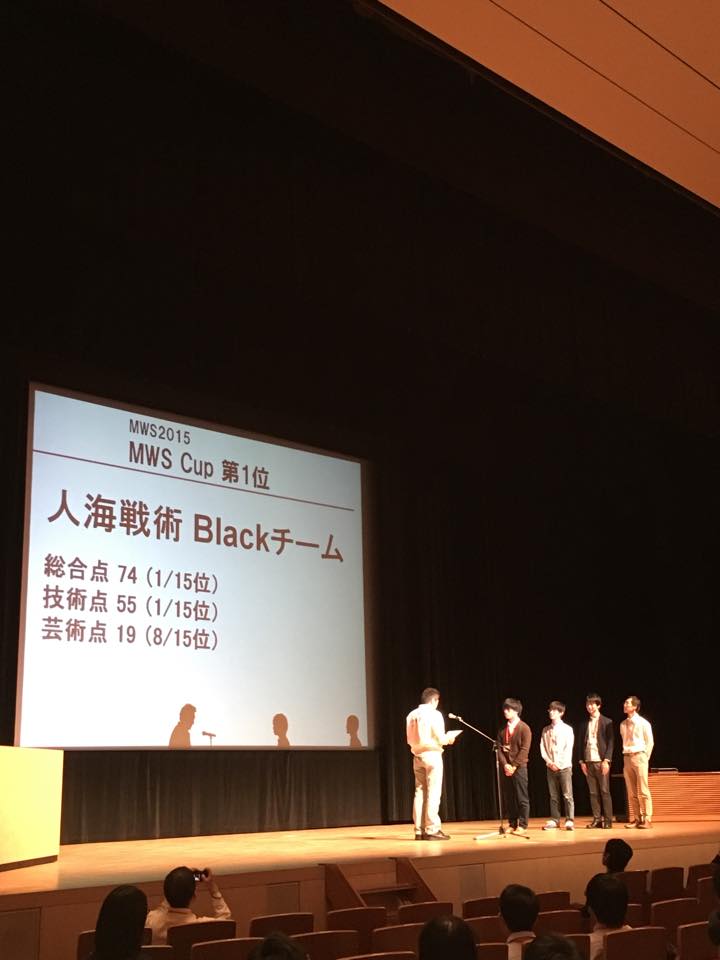 |
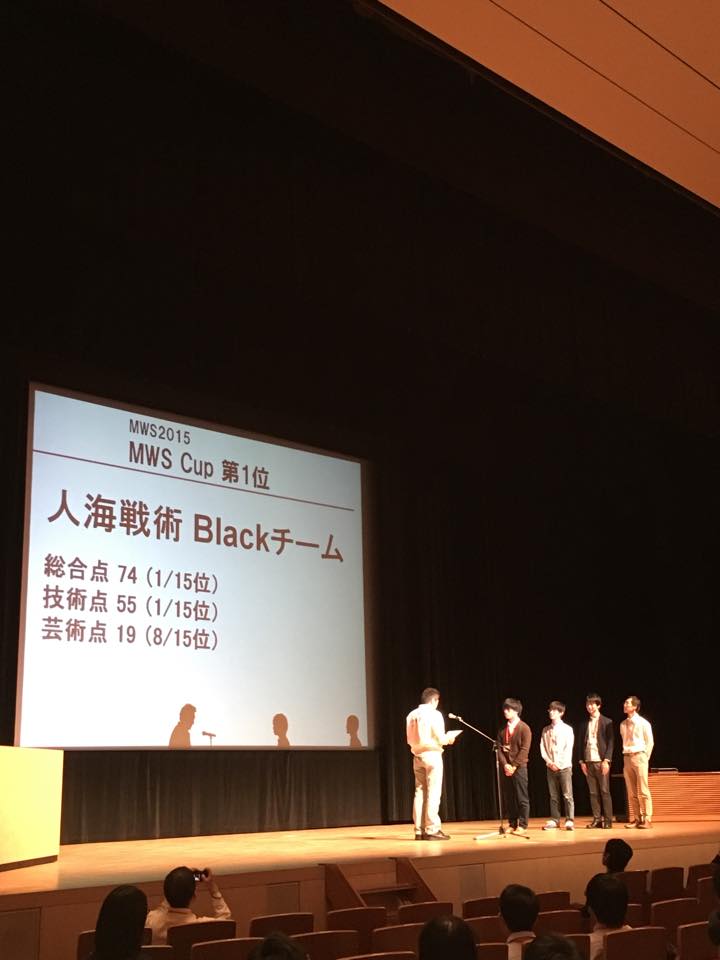
MWS Cup 2015 First Place Winner |
JINKAI-SENJUTSU Black Team |
74 (1) |
55 (1) |
19 (8) |
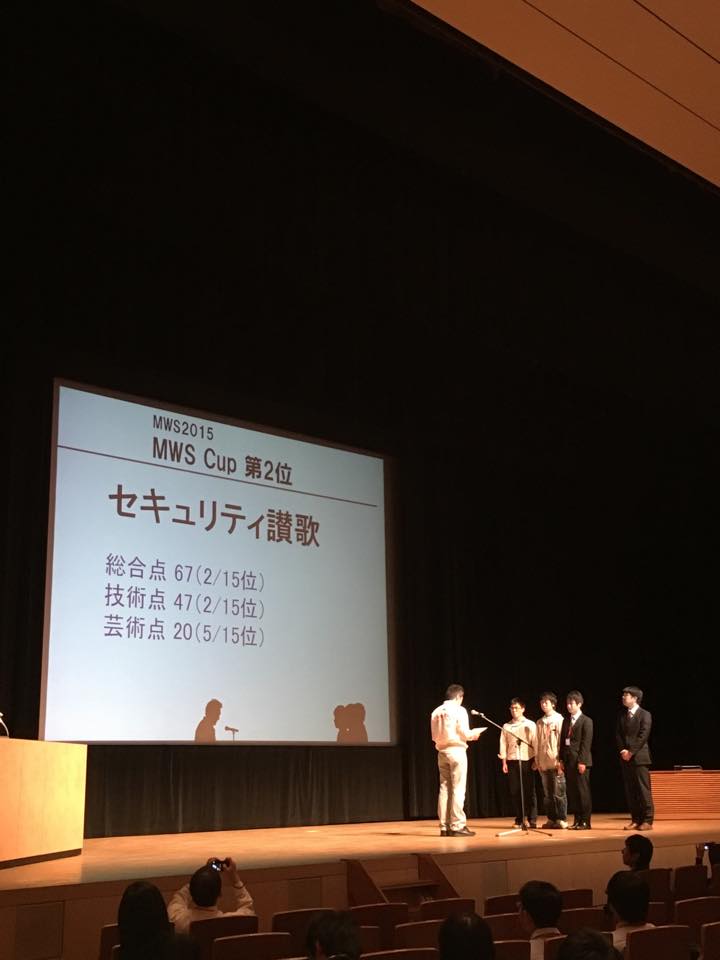 |
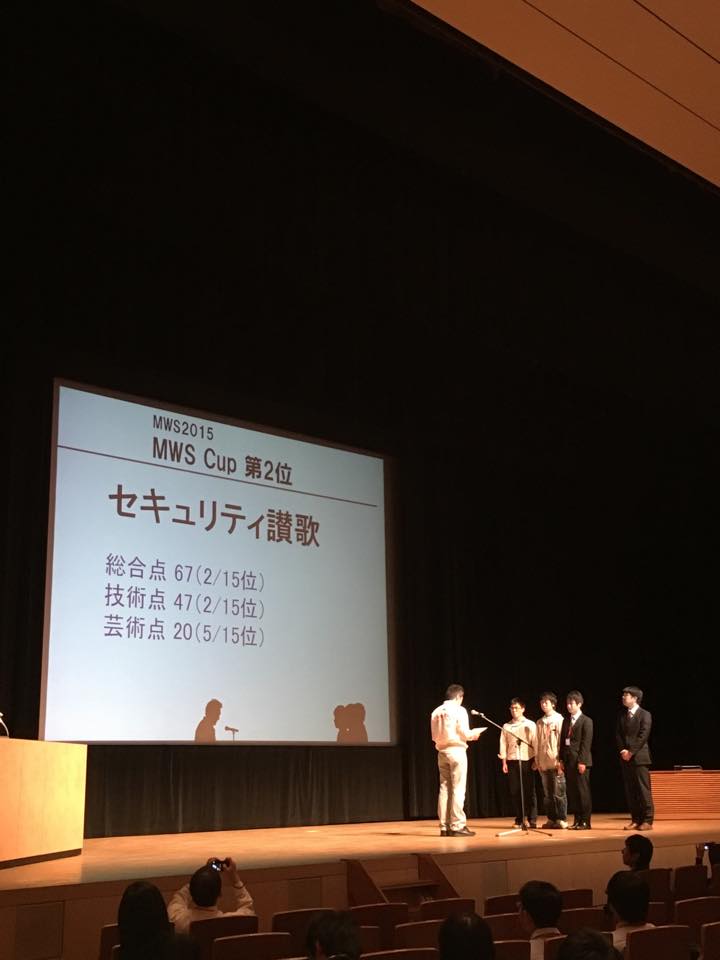
MWS Cup 2015 Second Place Winner |
Security SANKA |
67 (2) |
47 (2) |
20 (5) |
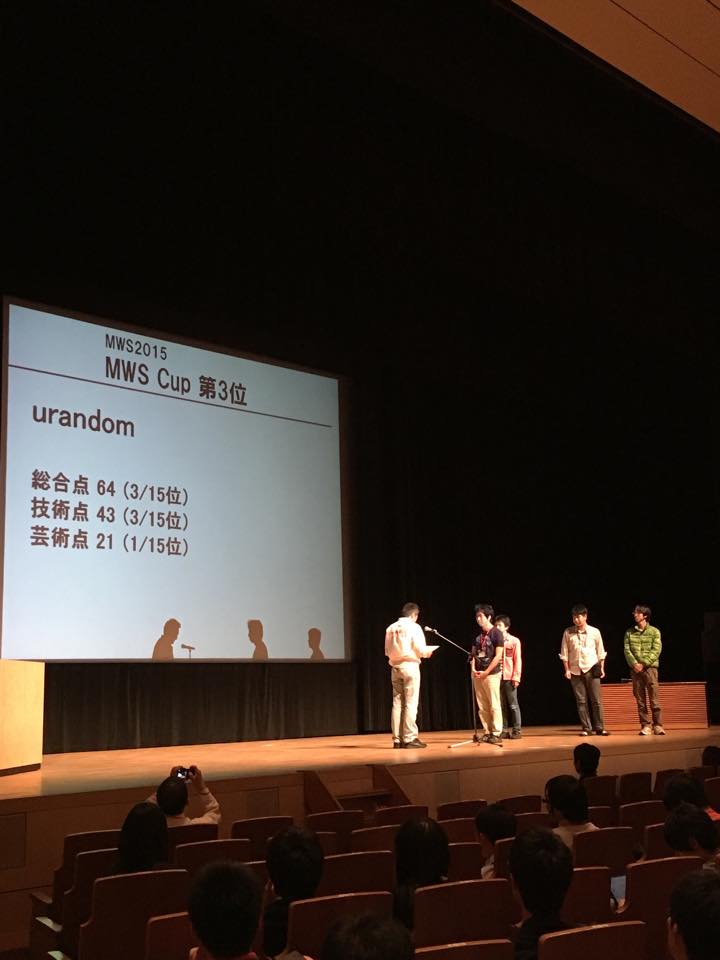 |
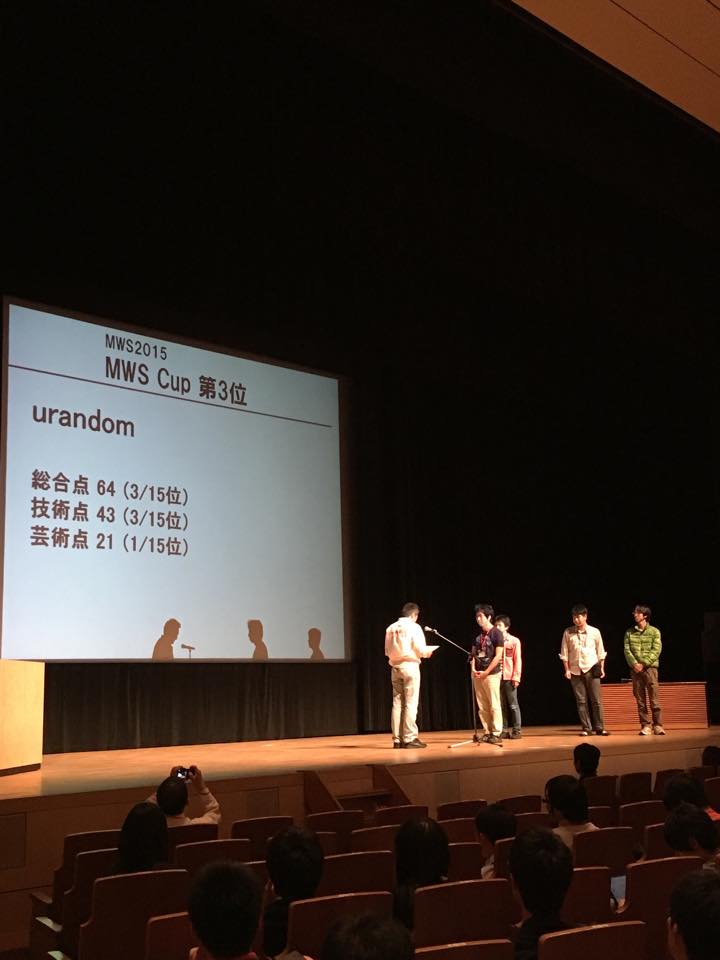
MWS Cup 2015 Third Place Winner |
urandom |
64 (3) |
43 (3) |
21 (1) |
 |
MWS Cup 2015 Planning Board Chair Special Prize |
JINKAI-SENJUTSU Black Team
Kazumi Ishibuchi (HIRT, Hitachi, Ltd.) |
MWS Cup 2015
 |
Briefing from a MWS Planning Board member, before the technical session. |
 |
Just after the beginning of the technical session. |
 |
Introduction from a MWS Planning Board member during the technical session. |
 |
Commentary to the Challenges from the authors (1). |
 |
Commentary to the Challenges from the authors (2). |
 |
Commentary to the Challenges from the authors (3). |
 |
Just before the end of the technical session. |
 |
Presentation session. |
 |
Evaluation of presentations. |
 |
MWS 2015 Manuscripts and Slides
- Symbols
- "*" : presenter
- "**" : student presenter
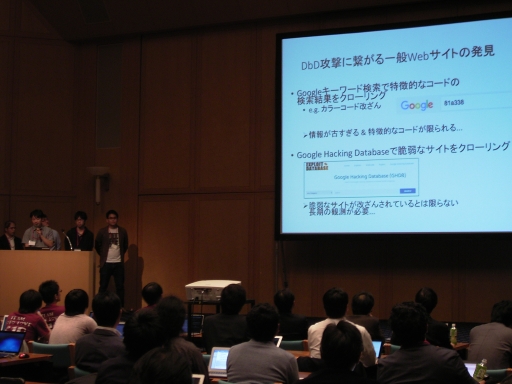
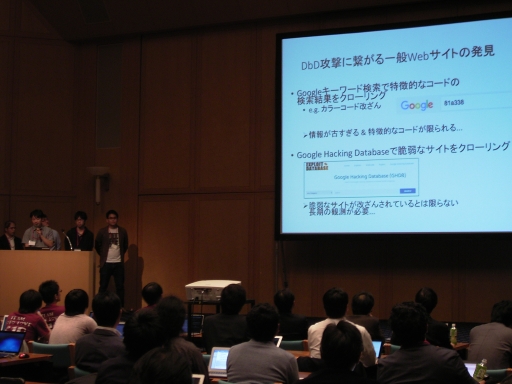
1A3: Drive-by Download Attack
(session chair: Makoto Iwamura)
1A3-1: Drive-by Download Detection Method based on Network Traffic Correlation
- * Seigo Terada (PFU LIMITED)
- Takashi Kobayashi (PFU LIMITED)
- Kazuhiro Koide (PFU LIMITED)
- Itsufumi Hato (PFU LIMITED)
- Mugen Setoguchi (PFU LIMITED)
- Keiji Michine (PFU LIMITED)
- Kouichi Yamashita (PFU LIMITED)
1A3-2: A method of preventing the malicious redirections of Web sites by transitions of HTTP communications and URL attribute information
- ** Yuma Sato (Graduate School of Systems Information Science, Future University Hakodate)
- Yoshitaka Nakamura (School of Systems Information Science, Future University Hakodate)
- Osamu Takahashi (School of Systems Information Science, Future University Hakodate)
1A3-3: The assessment of the effectiveness of cyber attack detection system for enterprise use
- * Masayoshi Shigeta (NTT DATA Corporation)
- Hisamichi Ohtani (NTT DATA Corporation)
- Shinichi Ohshima (NTT DATA Corporation)
1A3-4: Improving Cyber Attack Detection System To Adopt The Changing Of Exploit Kit
- * Hiroki Mashiko (NTT DATA Corporation)
- Hisamichi Ohtani (NTT DATA Corporation)
- Masayoshi Shigeta (NTT DATA Corporation)
1F4: Android
(session chair: Ayumu Kubota)
1F4-1: Studies on Risk Level Evaluation Schemes using APK Metadata
- * Takeshi Takahashi (National Institute of Information and Communications Technology)
- Tao Ban (National Institute of Information and Communications Technology)
- Takao Mimura (SecureBrain Corporation)
- Koji Nakao (National Institute of Information and Communications Technology)
1F4-2: A Large-scale Analysis of Cloned Android Apps
- ** Yuta Ishii (Waseda University)
- Takuya Watanabe (Waseda University)
- Mitsuaki Akiyama (NTT Secure Platform Laboratories)
- Tatsuya Mori (Waseda University)
1F4-3: An empirical study of Android APK disributuion sites using headless browser with navigation scripting
- * Ruo Ando (Network Security Institute, National Institute of Information and Communications Technology)
2A1: Drive-by Download Attack and Illegal Communication
(session chair: Yasuyuki Tanaka)
2A1-1: Detection of suspicious redirection using HTTP request sequence
- ** Sei Kudo (National Defense Academy)
- Tran Cong Manh (National Defense Academy)
- Yasuhiro Nakamura (National Defense Academy)
2A1-2: Detecting obfuscated malicious JavaScript based on
information-theoretic measures and novelty detection
- ** Jiawei Su (Graduate School of Environment and Information Sciences, Yokohama National University)
- Katsunari Yoshioka (Graduate School of Environment and Information Sciences / Institute of Advanced Sciences, Yokohama National University)
- Junji Shikata (Graduate School of Environment and Information Sciences / Institute of Advanced Sciences, Yokohama National University)
- Tsutomu Matsumoto (Graduate School of Environment and Information Sciences / Institute of Advanced Sciences, Yokohama National University)
2A1-3: A study for effectiveness of User-Agent for malware communication traffic detection
- * Tatsuya Ichida (Recruit Technologies Co.,Ltd.)
2A1-4: Automatic Generation of URL Regular Expression for Detecting Malicious Traffic
- * Susumu Serita (Hitachi, Ltd. Research & Development Group)
- Yasuhiro Fujii (Hitachi, Ltd. Research & Development Group)
- Tomo Kakuta (Hitachi Systems, Ltd.)
- Yoshitake Michiori (Hitachi Systems, Ltd.)
- Ohtori Tomoya (Hitachi Systems, Ltd.)
- Takeyasu Kishiro (Hitachi Systems, Ltd.)
- Masato Terada (Hitachi, Ltd. Research & Development Group)
2A3: Log Analysis
(session chair: Nobutaka Kawaguchi)
2A3-1: Characterizing Network Behavior of Malware: Toward Detecting New Malware Families with Network Monitoring
- ** Mitsuhiro Hatada (Graduate School of Fundamental Science and Engineering, Waseda University / NTT Communications Corporation)
- Tatsuya Mori (Graduate School of Fundamental Science and Engineering, Waseda University)
2A3-2: Detecting RAT Activity in Proxy Server Logs with Machine Learning
- * Mamoru Mimura (Institute of Information Security)
- Yuhei Otsubo (Institute of Information Security / National Police Agency)
- Hidehiko Tanaka (Institute of Information Security)
2A3-3: Method for detecting Malware based on clustering of time series information of infection behavior
- ** Ayaka Samejima (The University of Electro-Communications)
- Mitsuhiro Hatada (NTT Communications Corporation)
- Hiroshi Yoshiura (The University of Electro-Communications)
- Masatsugu Ichino (The University of Electro-Communications)
2A3-4: Darknet Traffic Analysis by Focusing on Variations in Dominant Traffic
- ** Toui Kanai (Tohoku Institute of Technology)
- Hiroshi Tsunoda (Tohoku Institute of Technology)
- Glenn Mansfield Keeni (Cyber Solutions Inc.)
2A4: Dynamic Analysis
(session chair: Yoshiaki Shiraishi)
2A4-1: Malware Communication Analysis using Dynamic Binary Instrumentationin Heterogeneous Analysis Environments for Stealthiness
- ** Yuma Kurogome (Faculty of Environment and Information Studies, Keio University)
- Keiji Takeda (Faculty of Environment and Information Studies, Keio University)
2A4-2: Correlating Experts' Malware Analysis Reports and Dynamic Malware Analysis Logs
- * Akinori Fujino (School of Fundamental Science and Engineering, Waseda University)
- Tatsuya Mori (School of Fundamental Science and Engineering, Waseda University)
2A4-3: Configuration study of the sandbox for the function improvement of environment-dependent malware analyzing system
- * Kichi Tokuyama (Hitachi, Ltd.)
- Tomohiro Shigemoto (Hitachi, Ltd.)
- Tetsuro Kito (Hitachi, Ltd.)
- Yoshiaki Isobe (Hitachi, Ltd.)
- Hirofumi Nakakoji (Hitachi, Ltd.)
2A4-4: A Note of Malware Detections in non-Windows using a Sandbox
- * Kiyohito Yamamoto (NTT Communications Corporation)
- Kousuke Hiraki (NTT Communications Corporation)
- Toshiaki Sudou (NTT Communications Corporation)
3A1: Endpoint
(session chair: Junichi Murakami)
3A1-1: Data Acquisition for Malware Analysis on Windows 7 x64
- ** Susumu Nakano (Ritsumeikan University)
- Yuto Otsuki (Ritsumeikan University)
- Shuhei Aketa (Ritsumeikan University)
- Eiji Takimoto (Ritsumeikan University)
- Shoichi Saito (Nagoya Institute of Technology)
- Koichi Mouri (Ritsumeikan University)
3A1-2: Implementation of System Call Tracer for Windows 10 x64
- ** Yuto Otsuki (Ritsumeikan University)
- Susumu Nakano (Ritsumeikan University)
- Shuhei Aketa (Ritsumeikan University)
- Eiji Takimoto (Ritsumeikan University)
- Shoichi Saito (Nagoya Institute of Technology)
- Koichi Mouri (Ritsumeikan University)
3A1-3: ROPGuard Bypass Prevention Method using Last Branch Recording Facilities
- ** Mitsunobu Tarao (Kanagawa Institute of Technology)
- Takeshi Okamoto (Kanagawa Institute of Technology)
3A1-4: Memory Access Control using Virtual Machine Monitor for Process Information Hiding
- * Masaya Sato (Graduate School of Natural Science and Technology, Okayama University)
- Toshihiro Yamauchi (Graduate School of Natural Science and Technology, Okayama University)
- Hideo Taniguchi (Graduate School of Natural Science and Technology, Okayama University)
3A2: Targeted Attack (1)
(session chair: Nobuyuki Kanaya)
3A2-1: Detection of Advanced Persistent Threat based on Cascade of Suspicious Activities over Multiple Internal Hosts
- * Nobutaka Kawaguchi (Hitachi, Ltd.)
- Mamoru Tsuichihara (Hitachi Advanced Systems, Ltd.)
- Kota Ideguchi (Hitachi, Ltd.)
- Yoshinobu Tanigawa (Hitachi, Ltd.)
- Hideyuki Tomimura (Hitachi, Ltd.)
3A2-2: Evaluation of Detection Method of Targeted Malware Displaying a Decoy Document
- * Yusuke Takahashi (NEC Corporation)
- Masafumi Watanabe (NEC Corporation / Graduate School of Environment and Information Sciences / Institute of Advanced Sciences, Yokohama National University)
- Shigeyoshi Shima (NEC Corporation / Graduate School of Environment and Information Sciences / Institute of Advanced Sciences, Yokohama National University)
- Katsunari Yoshioka (Graduate School of Environment and Information Sciences / Institute of Advanced Sciences, Yokohama National University)
3A2-3: Long-term Effectiveness of File Structure Inspection to Detect Malicious Document Files
- * Yuhei Otsubo (National Police Agency, Japan / Institute of Information Security)
- Mamoru Mimura (Institute of Information Security)
- Hidehiko Tanaka (Institute of Information Security)
3A2-4: A study on malware characteristics and its effects observed in targeted attacks
- * Ayaka Funakoshi (Japan Computer Emergency Response Team Coordination Center)
- Yu Nakamura (Japan Computer Emergency Response Team Coordination Center)
- Haruki Takeda (Japan Computer Emergency Response Team Coordination Center)
3A3: Targeted Attack (2), SECCON
(session chair: Takahiro Matsuki)
3A3-1: Analysis result of doc, pdf, zip file malware and its consideration
- ** Kosuke Yushita (Graduate School of Information Science, Nara Institute of Science and Technology)
- Shun'ichiro Ito (Graduate School of Information Science, Nara Institute of Science and Technology)
3A3-2: Web Mining System for Security Incidents Analysis
- * Takashi Yamaguchi (Tokyo University of Information Sciences, Department of Informatics)
- Koudai Tanide (Tokyo University of Information Sciences, Department of Informatics)
- Takeshi Misu (Tokyo University of Information Sciences, Graduate School of Informatics)
- Shinya Iwasaki (Tokyo University of Information Sciences, Graduate School of Informatics)
- Yorinori Kishimoto (Tokyo University of Information Sciences, Department of Informatics)
- Masaki Hanada (Tokyo University of Information Sciences, Department of Informatics)
- Eiji Nunohiro (Tokyo University of Information Sciences, Department of Informatics)
3A3-3: Early Detective Method of Remote Access Trojan by Host Base
- ** Daichi Adachi (School of Information Science, Japan Advanced Institute of Science and Technology)
- Kazumasa Omote (School of Information Science, Japan Advanced Institute of Science and Technology)
3A4: Malware Distribution and Malicious Contents
(session chair: Takahiro Kasama)
3A4-1: Trend analysis using spatio-temporal geographical information of the Malware distribution
- ** Shinya Iwasaki (Tokyo University of Information Sciences, Graduate School of Informatics)
- Takashi Yamaguchi (Tokyo University of Information Sciences, Department of Informatics)
- Eiji Nunohiro (Tokyo University of Information Sciences, Department of Informatics)
3A4-2: Analysis of spam mail containing malicious attachments using SpamTrap
- ** Masaki Shimura (School of Fundamental Science and Engineering, Waseda University)
- Mitsuhiro Hatada (NTT Communications Corporation)
- Tatsuya Mori (School of Fundamental Science and Engineering, Waseda University)
- Shigeki Goto (School of Fundamental Science and Engineering, Waseda University)
3A4-3: Analysis of Similarities among Malicious Contents Generated by Exploit Kit
- ** Yuya Konno (Tohoku Institute of Technology)
- Hiroshi Tsunoda (Tohoku Institute of Technology)
3E4: Traffic Observation
(session chair: Tatsuya Mori)
3E4-1: A Study of Port-Based Dynamic Darknet Monitoring
- * Masaki Narita (Tohoku Bunka Gakuen University, Faculty of Science and Technology)
- Keisuke Kamada (Iwate Prefectural University, Graduate School of Software and Information Science)
- Toyoo Takata (Iwate Prefectural University, Graduate School of Software and Information Science)
3E4-2: An apploach for controling IRCbot's activity using IPS
- ** Ryosuke Sakai (Faculty of Informatics, Kansai University)
- Takashi Kobayashi (Faculty of Informatics, Kansai University)
3E4-3: Method of Connecting System Call Trace Log and Packet Capture Data to Analyze Malware
- ** Yuki Okura (Ritsumeikan University)
- Yuto Otsuki (Ritsumeikan University)
- Yasuyuki Tanaka (NTT Communications Corporation)
- Shuhei Aketa (Ritsumeikan University)
- Eiji Takimoto (Ritsumeikan University)
- Koichi Mouri (Ritsumeikan University)
3E4-4: Overview of Research Data Set "Behavior Observable System 2015"
- * Masato Terada (Hitachi Ltd.)
- Kentaro Hori (Hitachi Ltd.)
- Yoshitaka Narishima (Hitachi Ltd.)
- Ryohei Yoshino (Trend Micro Incorporated)
- Kenta Hagihara (Trend Micro Incorporated)
3E4-5: Development of Adaptive Event-Monitoring System for DDoS Attacks
- ** Nobuaki Furutani (Guraduate School of Engineering,Kobe University)
- Jun Kitazono (Guraduate School of Engineering,Kobe University)
- Seiichi Ozawa (Guraduate School of Engineering,Kobe University)
- Tao Ban (National Institute of Information and Communications Technology)
- Junji Nakazato (National Institute of Information and Communications Technology)
- Jumpei Shimamura (clwit Inc.)
Contact us
If you have any questions, please contact: csecreg  sdl.hitachi.co.jp
sdl.hitachi.co.jp
Published: 0:15 2015/06/02
Last Update: 0:15 2015/06/02
Copyright 2015 The IPSJ, Information Processing Society of Japan, All rights reserved.


 sdl.hitachi.co.jp
sdl.hitachi.co.jp