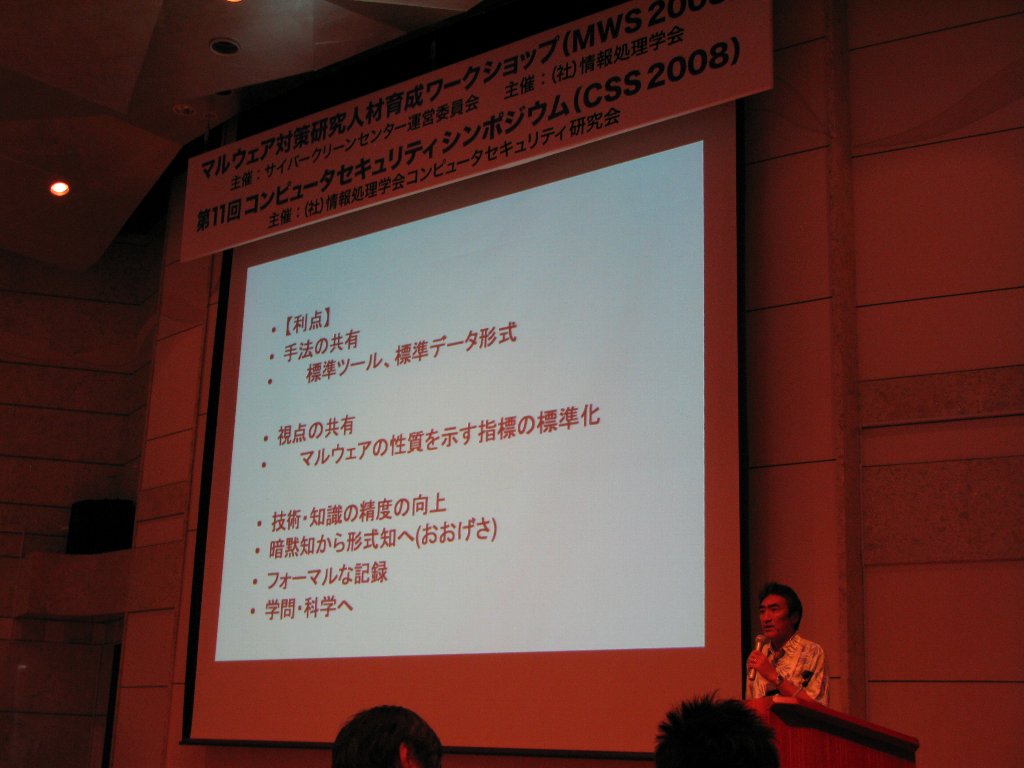
anti Malware engineering WorkShop 2008 (MWS 2008)
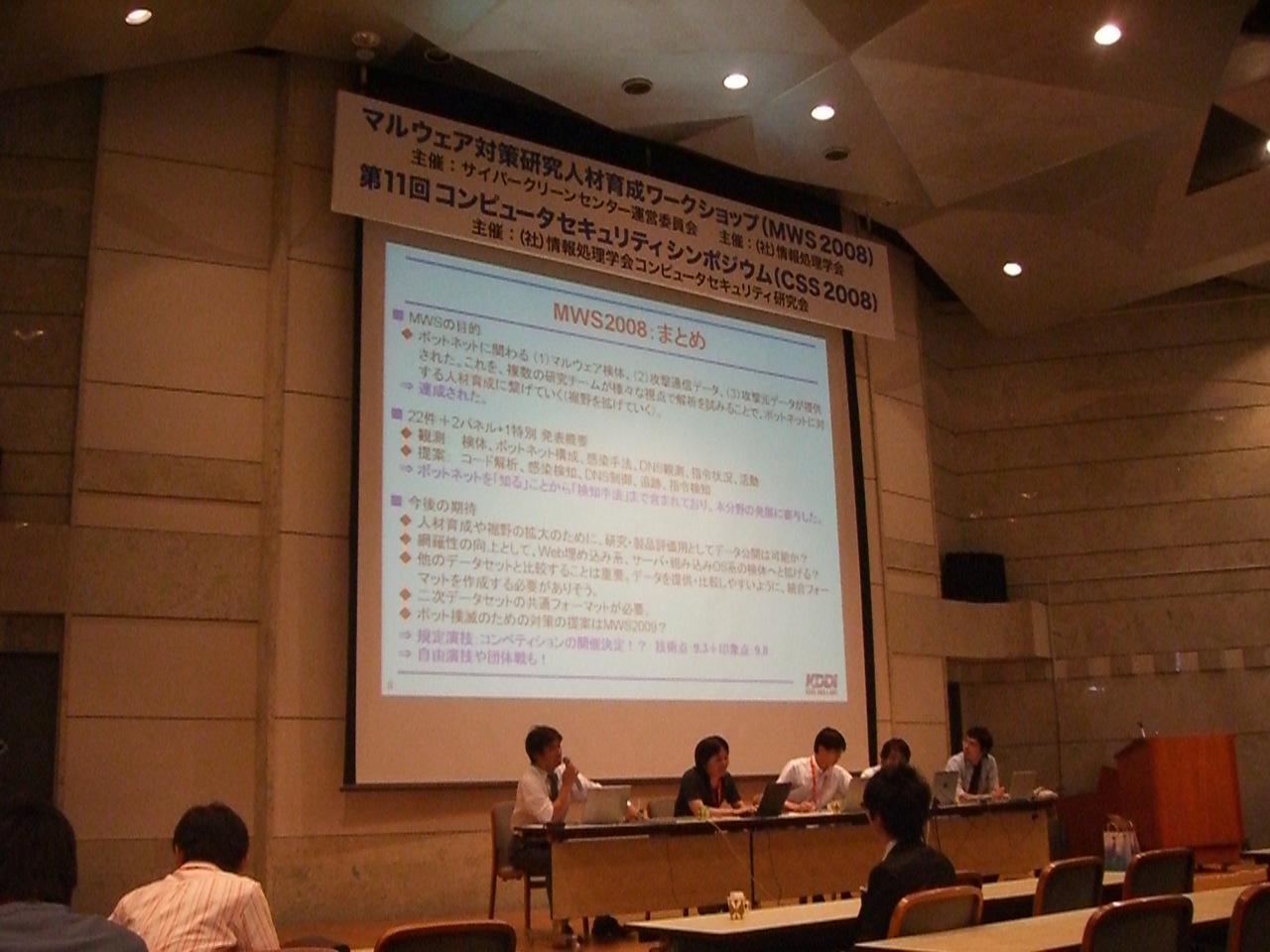
MWS2008
Okinawa Convention Center, Okinawa, Japan
October 8 - 10, 2008
| Date | Time | MWS2008 | CSS2008 |
| 10/8(Wed) | 12:10 - 13:50 (1:40) |
Session M1 Captured Data |
Session 1 |
| 14:05 - 15:45 (1:40) |
Session M2 Captured Data |
Session 2 | |
| 16:00 - 17:00 | Invite Session 1 | ||
| 18:00 - 20:00 | Candle Star Session (CSS×2.0) | ||
| 10/9(Thu) | 9:00 - 10:40 (1:40) |
Session M3 Access Log |
Session 3 |
| 10:55 - 12:35 (1:40) |
Session M4 Access Log |
Session 4 | |
| 13:35 - 14:45 | Invite Session 2 | ||
| 15:00 - 16:40 (1:40) |
Session M5 Panel Discussion 1 |
Session 5 | |
| 16:55 - 17:55 | Demo Session | ||
| 18:30 - 21:00 | MWS2008/CSS2008 Social Event | ||
| 10/10(Fri) | 9:00 - 10:40 (1:40) |
Session M6 Malware samples |
Session 6 |
| 10:55 - 12:35 (1:40) |
Session M7 CCC activities |
Session 7 | |
| 13:35 - 14:55 (1:20) |
Session M8 Panel Discussion 2 |
Session 8 | |
| 15:10 - 16:50 (1:40) |
------------ | Session 9 | |
Oct. 8, 2008
Session M1: Captured data of attacks: The detection of BOT infections (1) Chair: Satoru NORITAKE (Telecom-ISAC Japan) 12:10 - 12:30 Opening 12:30 - 13:50 Session M1
Opening
Yoichi SHINODA (Japan Advanced Institute of Science and Technology)(National Institute of Information and Communications Technology)1001: Feasibility Assessment of IPS based on Analyzing and Classifying Shellcode
Shoichi SAITO (Nagoya Institute of Technology), Tetsutaro UEHARA (Kyoto University), Tetsuya SHIMODAIRA (Nagoya Institute of Technology) and Hiroshi MATSUO (Nagoya Institute of Technology)[Abstract] Some Host-based Intrusion Prevention Systems (IPS) observe Windows APIs and system calls issued by the target programs and detect their anomalous behaviour to prevent intrusions by malwares. Most of such malwares firstly exploit vulnerability of the system to feed small programs called shell codes. These shell code preempt processes to pull the main bodies of malwares. The target to detect anomalies is such behavior of the malware. In this paper, the authors analize and classify actual shell codes obtained from CCC DATAset 2008 as the basis to develop an IPS.
[Manuscript in PDF(Japanese)]
1021: A result of Malware analysis in CSS2008 dataset
Soma KATSUTE (Kobe University), Koki YASUMOTO (Naruto University of Education), Naoto SONE (Kobe University) and Masakatu MORII (Kobe University)[Abstract] In this paper, we restore executable files of the malware from the communication data captured by the honey pot. In addition, we apply our classi cation technique of the malware and static analyses of the malware to them. By our analysis, malwares assumed to be UNKNOWN were classi ed into small groups with some similarities.
[Manuscript in PDF(Japanese)]
1008: Study for Detecting Bot-Infected PC based on behavior of DNS query
Yoshiki Higashikado (Fujitsu Laboratories LTD.) and Satoru Torii (Fujitsu Laboratories LTD.)[Abstract] We analyzed the attack communication data of CCC DATAset 2008, focusing to DNS query which the honeypot sends to. In this paper, we clarify the feature of the DNS query from infection of bot to activity. The feasibility study of the detection method was also presented. As a result, unknown activity of bot has been extracted, such as solving various hosts' name and an internal hosts’ name. We think that those feature are valuable, as they means the communication of early stage of infection and they cannot be got by the code analysis.
[Manuscript in PDF(Japanese)]
1019: Improving Isolated Sandbox using Fake DNS Server
Shinsuke MIWA (National Institute of Information and Communications Technology), Daisuke MIYAMOTO (Nara Institute of Science and Technology), Hiroaki HAZEYAMA (Nara Institute of Science and Technology), Daisuke INOUE (National Institute of Information and Communications Technology) and Youki KADOBAYASHI (Nara Institute of Science and Technology)(National Institute of Information and Communications Technology)[Abstract] Recent viruses, worms, and bots, called malwares, often have anti-analysis functions such as mechanisms that confirm connectivity to certain Internet hosts. Although, to avoid any impacts to/from the Internet, we conclude that analyzing environments should be disconnected from the Internet. We discuss how malwares can be kept alive in an analyzing environment by disabling their anti-analyzing mechanisms on isolated sandboxes. To reconcile these crosspurposes, we designed an isolated sandbox with fake DNS server that called “NINFD”. We implemented a prototype system and conducted an experiment to test the efficiency of our fake DNS server.
[Manuscript in PDF(Japanese)]
Session M2: Captured data of attacks: The detection of BOT infections (2) Chair: Akifumi TANAKA (Telecom-ISAC Japan) 14:05 - 15:45
1009: A Study of Bot Activities Focused on State Transition of Communications
Masayoshi MIZUTANI (Keio University), Keiji TAKEDA (Keio University) and Jun MURAI (Keio University)[Abstract] This paper describes a study of controlled malicious softwares (Bots) activities included in CCC DATAset 2008 based on our state transition model of common bots. Bot variants are generated for a shorter period than traditional computer viruses and bot’s features are frequently changed. We focused common sequence of bot’s actions and built a state transition model soon after bot infections to detect new bot variants. In this paper, we analyzed CCC DATAset 2008 based on our model and confirmed that bots activities are accooding to our model if bot communications are not failure.
[Manuscript in PDF(Japanese)]

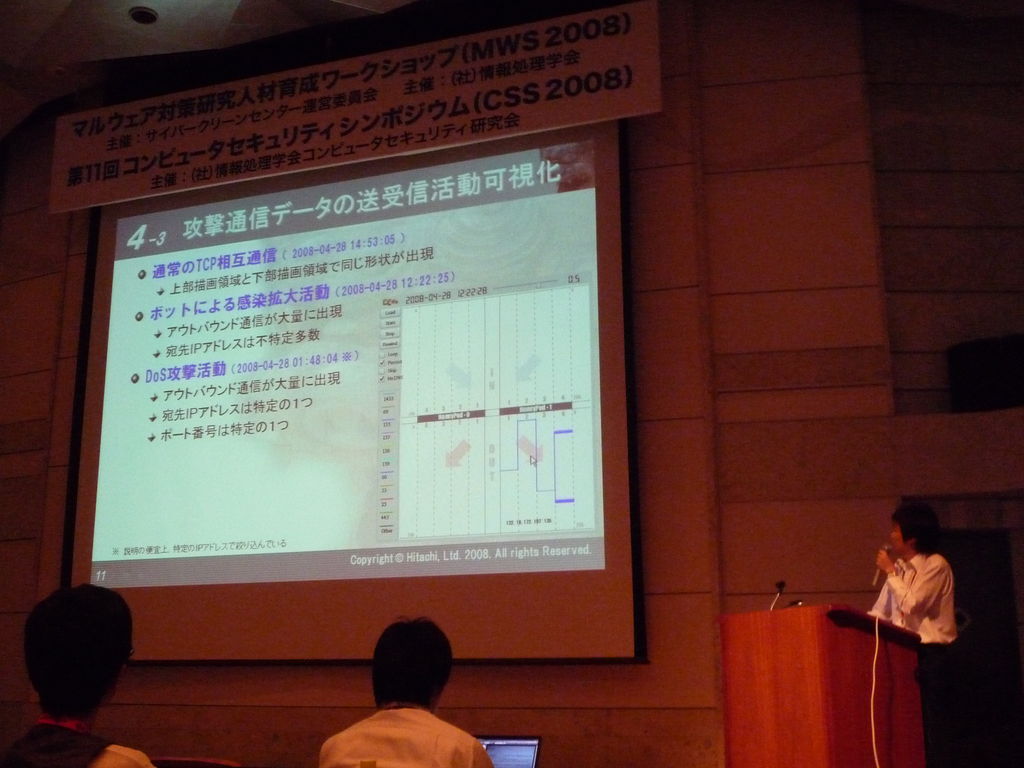
1017: Visualization of the commands and responses of botnets focused on the synchronization of packet transmission
Hirofumi NAKAKOJI (Hitachi Ltd.), Nobutaka KAWAGUCHI (Hitachi Ltd.), Tetsuro KITO (Hitachi Ltd.), Tomohiro KOBORI (Tokai University), Hiroaki KIKUCHI (Tokai University) and Masato TERADA (Hitachi Ltd.)[Abstract] In recent years, many bots has a large number of variants and uses code obfuscation and encryption channels to evade existing IDS and anti-virus software. In particular, encryption channels can prevent network-based approaches from analyzing packet contents, and therefore demand for the development of new detection methods that does not rely on pattern matching is increasing. In this research, we visualize the communication of bots and reveal the features of their activities. Then, we extract packets related to the bots activities from traffic based on the features, and identify the hosts infected by the bots and the command servers.
[Manuscript in PDF(Japanese)]
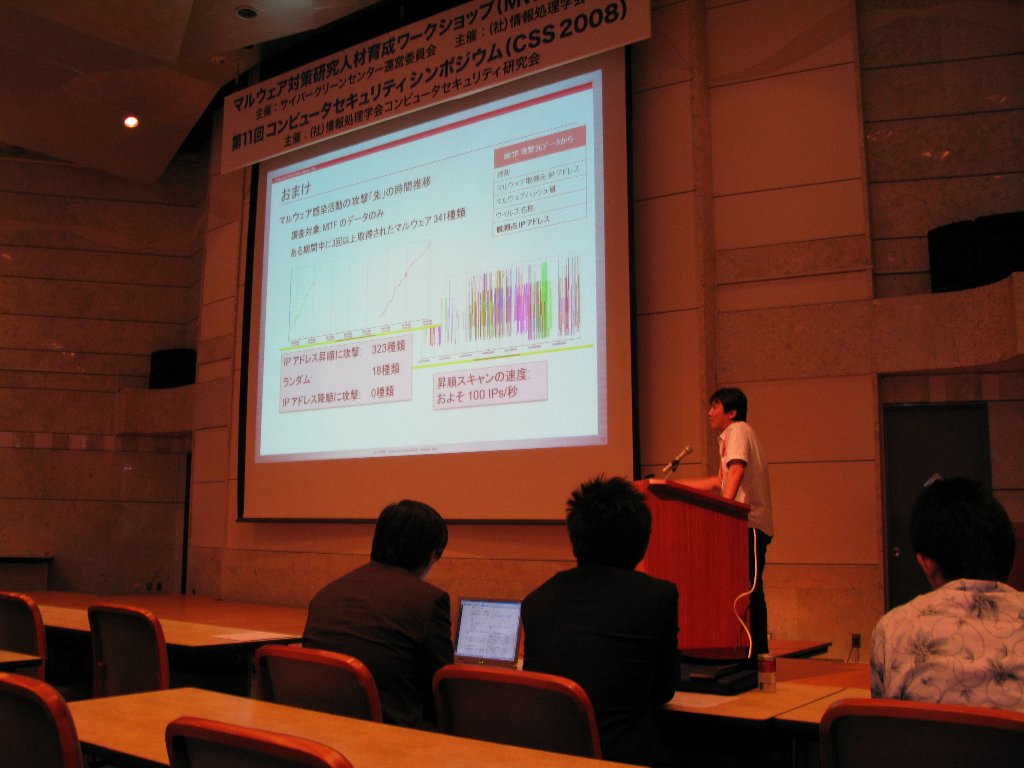
1011: Visualization of Chain Infection and Guess of Sample Classification by Time Series Analysis
Takahiro MATSUKI (Little eArth Corporation Co., Ltd.)[Abstract] The infection of chain-driven malware is increasing through the downloader, presently. In this paper, we’ve analysed traffic data and sources of attack in a way of time series and visualization. In addition, we’ve identified the perspective of the infection of chaindriven malware.
[Manuscript in PDF(Japanese)]

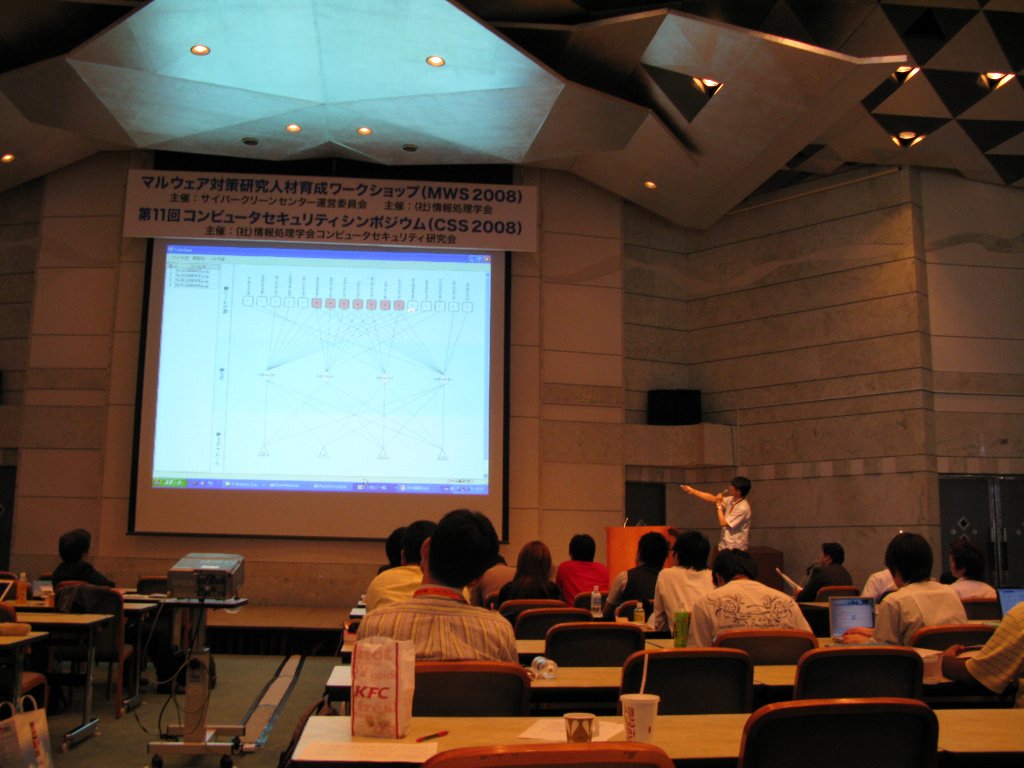
1015: Plan of Multistep Pursuit System of Botnet And Use Technique of CCC DATAset 2008
Hajime MIHARA (Tokyo Denki University), Takaaki NAGUMO (Tokyo Denki University), Yuki ASHINO (Tokyo Denki University), Tetsutarou UEHARA (Kyoto University) and Ryoichi SASAKI (Tokyo Denki University)[Abstract] Recentry, damage caused by the botnet becomes a big problem. There is a problem that the other bot PCs are produced, even if one bot PC could be specified. Therefore, it is not a fundamental solution. To solve this problem, authors propose the multistep trace back system that pursues not only bot PCs but the C&C server and Harder. Moreover, authors describe the C&C server detection technique using Data set for research CCC DATAset 2008 for the second step in this system.
[Manuscript in PDF(Japanese)]
1012: Analysis of Robust Mechanisms into Botnet and Code Set
Keisuke TAKEMORI (KDDI R&D Laboratories Inc.), Takamasa ISOHARA (KDDI R&D Laboratories Inc.), Yutaka MIYAKE (KDDI R&D Laboratories Inc.) and Masakatsu NISHIGAKI (Shizuoka University)[Abstract] A botnet is composed of multiple command and control (C&C) servers to distribute bot codes and control commands efficiently. A scheme of parallel C&C servers persists against an antivirus (AV) software. It is hard to remove the all bot codes from an infected PC because of the multiple infection, the multiple functions, the update to new code, and the invalidation of AV functions. In this paper, we investigate into the robust mechanisms of the botnet: (i) the parallel structure of the C&C severs and (ii) the parallel management for the bot code on the Internet. Also, we investigate into the robust mechanisms of the bot code: (iii) the number of infected bot codes, (iv) the variety of bot functions, (v) the update function, and (vi) the anti AV technique.
[Manuscript in PDF(Japanese)]
Oct. 9, 2008
Session M3: Access log of attacks: The overall trend of BOT activities (1) Chair: Toshiaki KOKADO (Information Technology Promotion Agency, Japan) 9:00 - 10:40
1018: Visualization of malware attacks based on their lifecycle
Fumihiko KOZAKURA (Fujitsu Laboratories LTD.), Hiroshi TSUDA (Fujitsu Laboratories LTD.), and Satoru TORII (Fujitsu Laboratories LTD.)[Abstract] In the attack host log of CCC DATAset 2008, we investigate the malware activities before and after they are named by virus vendors and visualize the relation with attack host, area, etc.
[Manuscript in PDF(Japanese)]
1002: Analysis of CCC DATAset 2008 using OLAP and Automated malware variant classification
Dai NAGATA (Institute of Information Security), Keiichi HORIAI (Institute of Information Security) and Hidehiko TANAKA (Institute of Information Security)[Abstract] The OLAP is a method to analyze multi-dimensional data in the area such as Business Intelligence. In this report, we describe the method of applying OLAP to the analysis of CCC DATAset 2008 and its results. Authors have been developing an automated malware analyzing system. We have adopted the system to analyze the specified malware in the CCC DATAset 2008 and we describe the outline of the system and the obtained results.
[Manuscript in PDF(Japanese)]
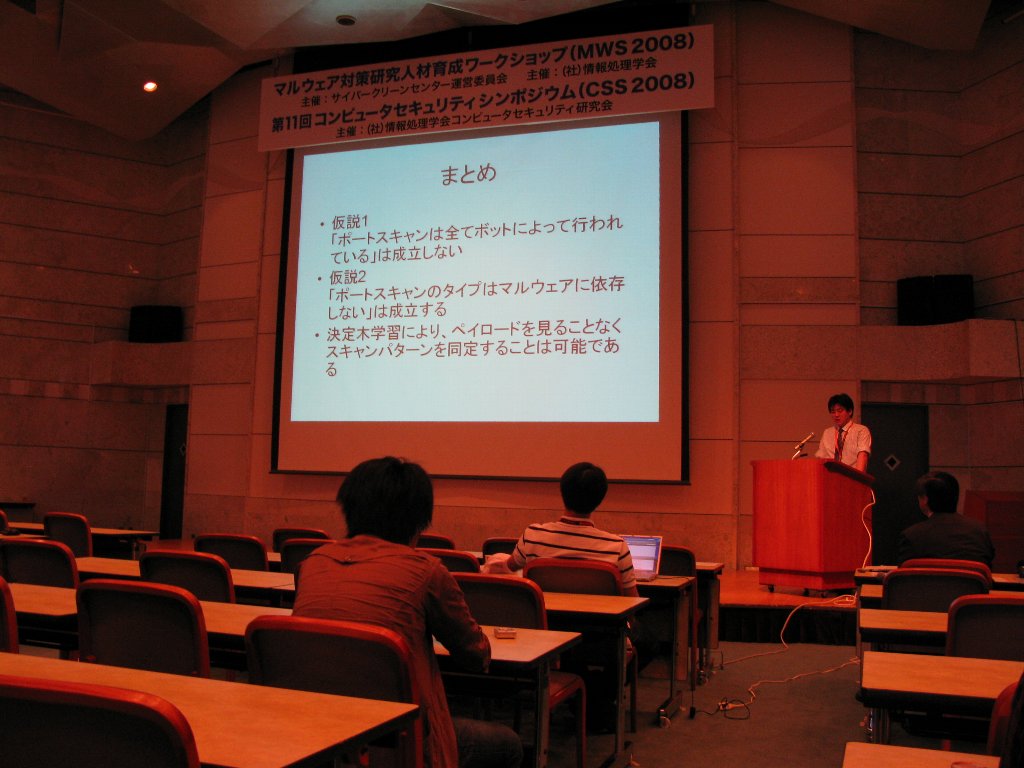
1003: Interrelation between Interactive and Non-interaction Sensors
Tomohiro KOBORI (Tokai University) Hiroaki KIKUCHI (Tokai University) and Masato TERADA (Hitachi, Ltd.)[Abstract] Our study aims to clarify if the port-scanning packets sent from bot-infected hosts are identical to the packets obserbed by distributed non-interactive sensors. Based on the statistical propeties of the CCC DATASet and the ISDAS, we show the decision trees to automatically identify port-scanning strategies, random or sequential without investigating the payload of given packets. The main result is that port-scanning behaviors are independent from the malware infected to the scanners.
[Manuscript in PDF(Japanese)]
1010: Analysis of Bot Activities Based on Malware Transfer Records
Akira KANAI (Keio University), Masayoshi MIZUTANI (Keio University), Keiji TAKEDA (Keio University) and Jun MURAI (Keio University)[Abstract] Bot threatens Internet users' security with malicious behaviors. The new varieties of botware appear everyday. Since those bots conceal their existences and activities, it is difficult to defend from them. Properties of the general botware are not well known, although knowing their trends is necessary in taking actions against them. In this paper, the event logs of malware activities, on some hosts within Japan, were analyzed. By classifying them in terms of geographic locations where the bots actually came from, relationships were discovered between the infections and Internet trends in Japan, such as network topologies and traffic trends. Also, it was found that the attackers update their botware often enough, to avoid from being detected by anti-malware solutions.
[Manuscript in PDF(Japanese)]
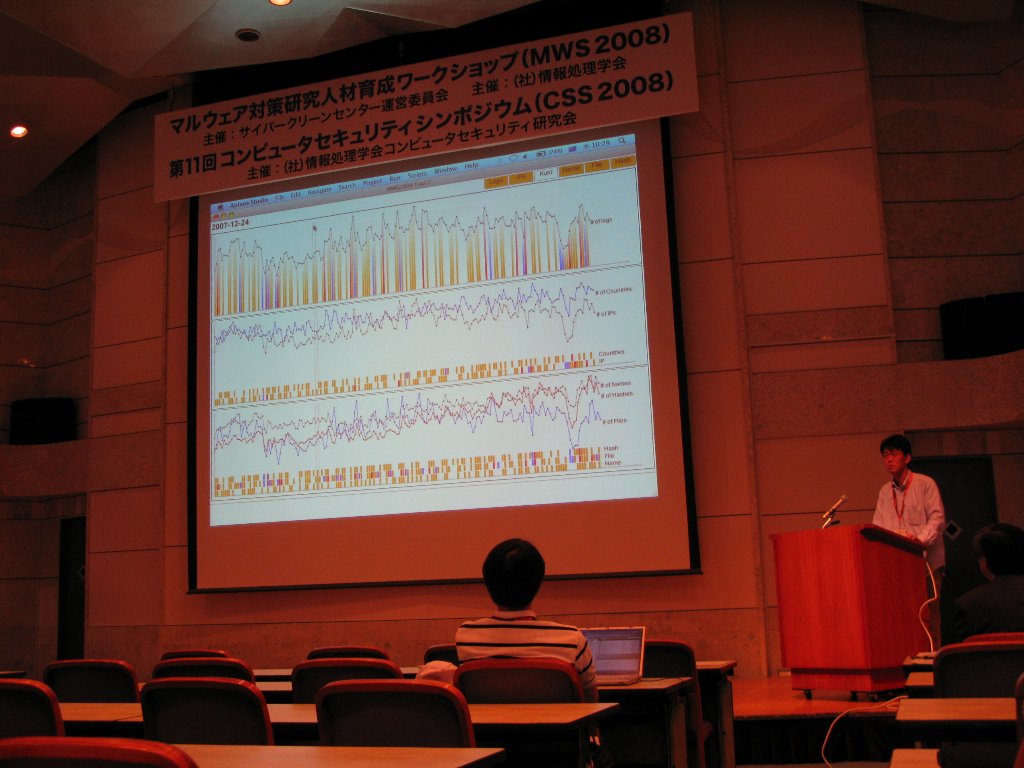
1014: A Proposal of a User Interface that Assists Human Inspectors in Understanding Attack Source Log in Honeypots
Tetsuji TAKADA (National Institute of Advanced Industrial Science and Technology) and Hideki KOIKE (University of Electro-Communications)[Abstract] In this paper, we consider that what kind of requirements are needed for a user interface for assisting a human inspector in investigating log information from honeypots. And we reach a conclusion that there are four requirements: 1) A system extracts a trend information from a log as a global view. 2) A system represents data using a graph or another visual representation for reducing recognition load. 3) A system provides users with an incremental investigation method from a global view to a detail view. 4) A system provides users with an interactive function to support trial and error inspection. Based on the consideration, we developed a prototype log browsing system. We also explain a log inspection example using the prototype system. Therefore, it makes clear that the prototype system has a potential to assist in log inspection by a human.
[Manuscript in PDF(Japanese)]
Session M4: Access log of attacks: The overall trend of BOT activities (2)
Chair: Tomomitsu MOCHIZUKI (Information Technology Promotion Agency, Japan)
10:55 - 11:55 Session M4
11:55 - 12:35 General Chair Session
Yoichi SHINODA (Japan Advanced Institute of Science and Technology)
(National Institute of Information and Communications Technology)
1004: A Study of Botnet Activity Analysis using Multiple Monitoring Data
Mitsuhiro HATADA (NTT Communications Corporation) and Masato Terada (Chuo University)[Abstract] Today, botnet activities are major concern such as various infection method, massive spreading E-mail spam, DDoS attacks and construction of phishing site. And it is hard to understand the activities of botnet by its rich functions and high practical operation. This paper shows some results of analysis about botnet activities using multiple monitoring data.
[Manuscript in PDF(Japanese)]
1020: A Comparison Between Malware Observations from Honeypot Networks of Different Sizes
Tadaaki NAGAO (Internet Initiative Japan Inc.), Hiroshi SUZUKI (Internet Initiative Japan Inc.) and Mamoru SAITO (Internet Initiative Japan Inc.)[Abstract] In this paper, we compare two observational data sets of malware infection activity, one of which is CCC DATAset 2008 Attack Source Data from wide honeypot network and another data set from IIJ's locally installed honeypot network. We study and discuss differences observed between them.
[Manuscript in PDF(Japanese)]
1005: Analysis of Malware Activities Based on Download Hosts
Hiroki ISHII (Okayama University), Kazuya SATO (Okayama University) and Toshihiro TABATA (Okayama University)[Abstract] Recently, damage caused by bot is one of serious problem. The bot is a kind of malware. Therefore, there are studies based on infection behavior of malware through network and on the information of the bot infected state. On the other hand, there is few studies based on download hosts. In this paper, we describe an analysis of malware activities analyzed from the attack data of "CCC DATAset 2008". Specifically, we focus on the relation between download hosts and malware and the characteristics of malware activities.
[Manuscript in PDF(Japanese)]
General Chair Session
Yoichi SHINODA (Japan Advanced Institute of Science and Technology)(National Institute of Information and Communications Technology)
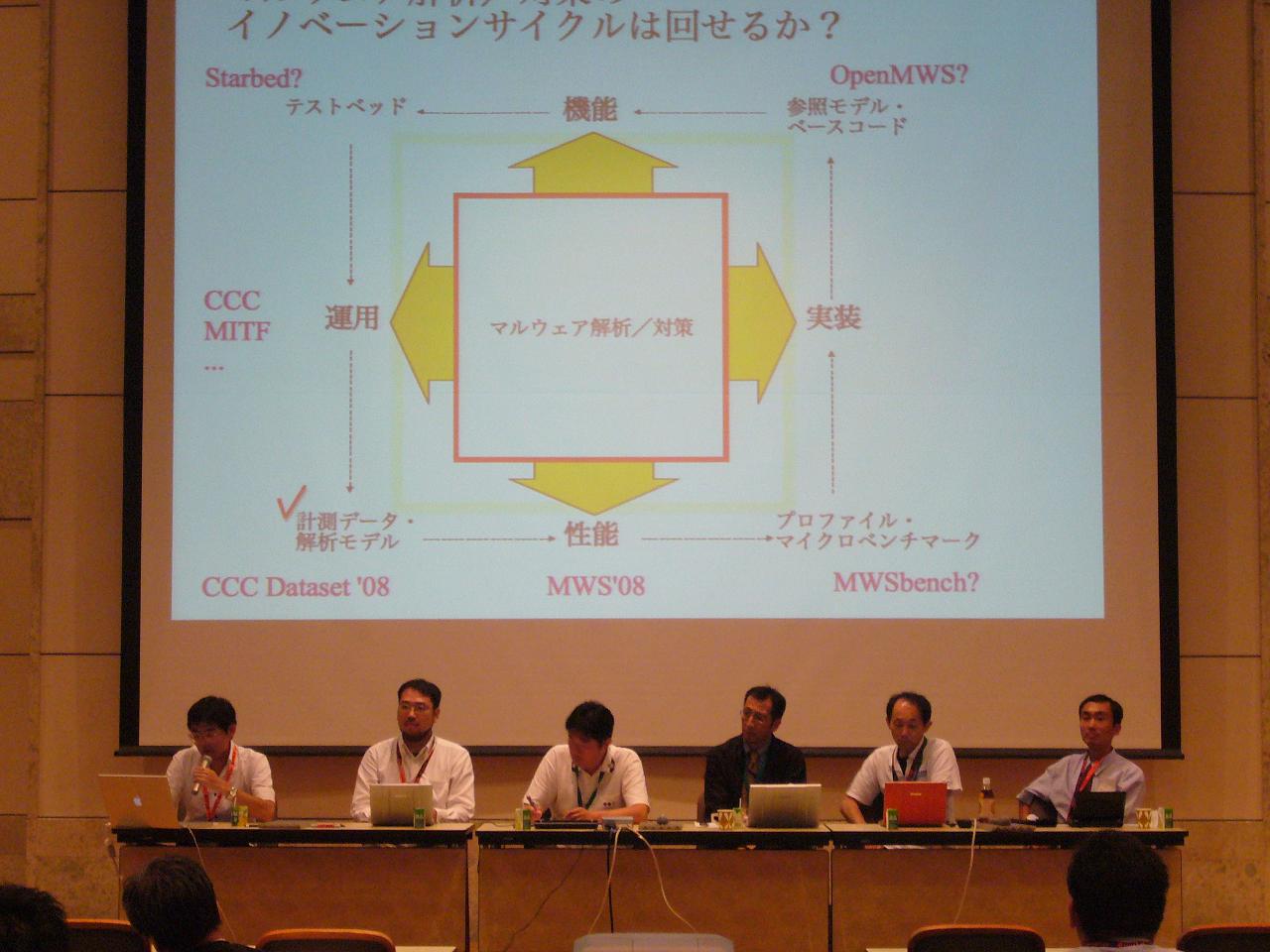
Session M5: Panel Discussion 1
Coordinator: Youki KADOBAYASHI (Nara Institute of Science and Technology)
(National Institute of Information and Communications Technology)
15:00 - 16:40
Oct. 10, 2008
Session M6: Malware samples: The dynamic/static analysis of BOTs Chair: Takashi MANABE (JPCERT Coordination Center) 9:00 - 10:40
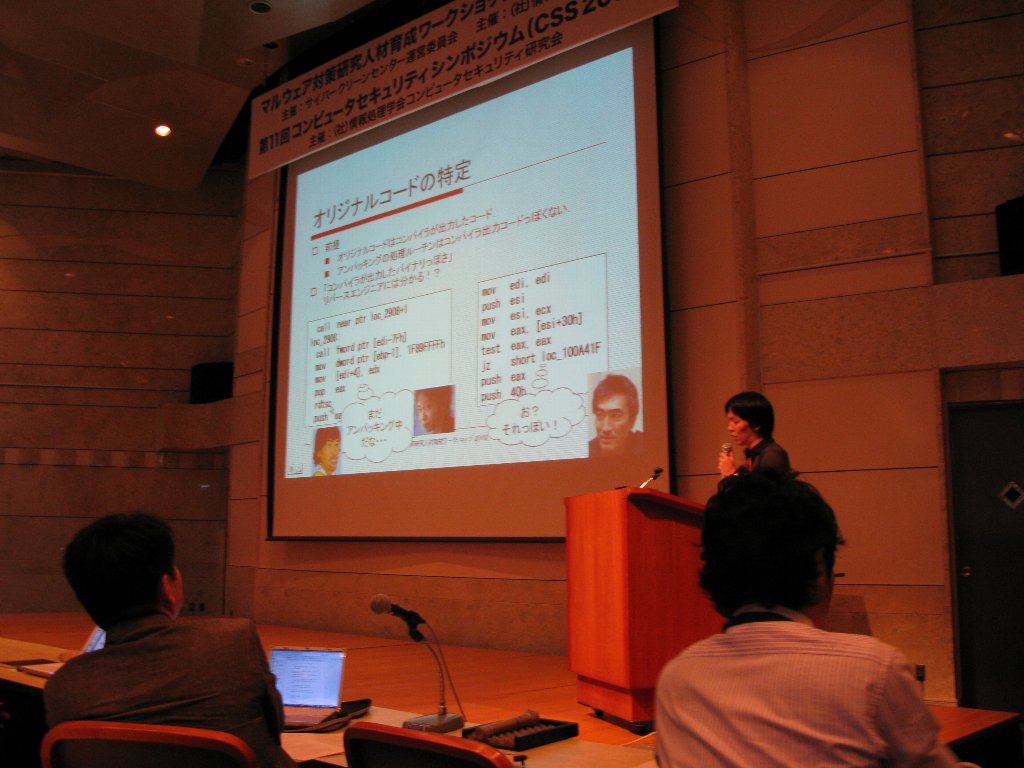
1006: Unpacking based on the likelihood of the compiled code model
Makoto IWAMURA (NTT Information Sharing Platform Laboratories), Mitsutaka ITOH (NTT Information Sharing Platform Laboratories) and Yoichi MURAOKA (Waseda University)[Abstract] In this paper, we propose a novel unpacking tool which can automatically extract the original code of a packed malware. A conventional tool hooking page-fault handler cannot run on the virtual machine which does not correctly implement TLB. Compared with it, our tool can run on it by more sophisticated monitor, which do not need TLB, for memory access. Additionally, even if the malware were multiple-packed i.e., two or more candidates of the original code were extracted by the previous process, our tool can specify the original code of a malware by calculating the likelihood of the compiled code model from given candidates. Experimental results with the malware sample of CCC DATAset 2008 show that our tool could extract some code regions as the candidates and specify the original code from them.
[Manuscript in PDF(Japanese)]
1022: A feasibility study of bot detection based on capturing self-initiated READ/DELETE behavior
Takahiro SAKAI (Shizuoka University), Takumi NAGAYA (Shizuoka University), Keisuke TAKEMORI (KDDI R&D Laboratories) and Masakatsu NISHIGAKI (Shizuoka University)[Abstract] Bot detection after being infected is usually difficult, since bot hides itself on the infected computer. Thus, it is preferable to capture the moment of bot infection. With regard to the way of infecting computer, bot is similar to worm. In other words, it is expected that the existing worm detection schemes can be applied to bot detection. For worm detection, we have already proposed a scheme based on capturing "self-initiated READ" behavior, which could be applicable to a variety of worms including unknown worms. Therefore this paper investigates how effectively bot infection can be detected by checking its self-READ behavior. In addition, we know that many bot removes itself from computer to cover up its infection. So, this paper focuses also on using its "self-DELETE behavior" to capture bot infection.
[Manuscript in PDF(Japanese)]
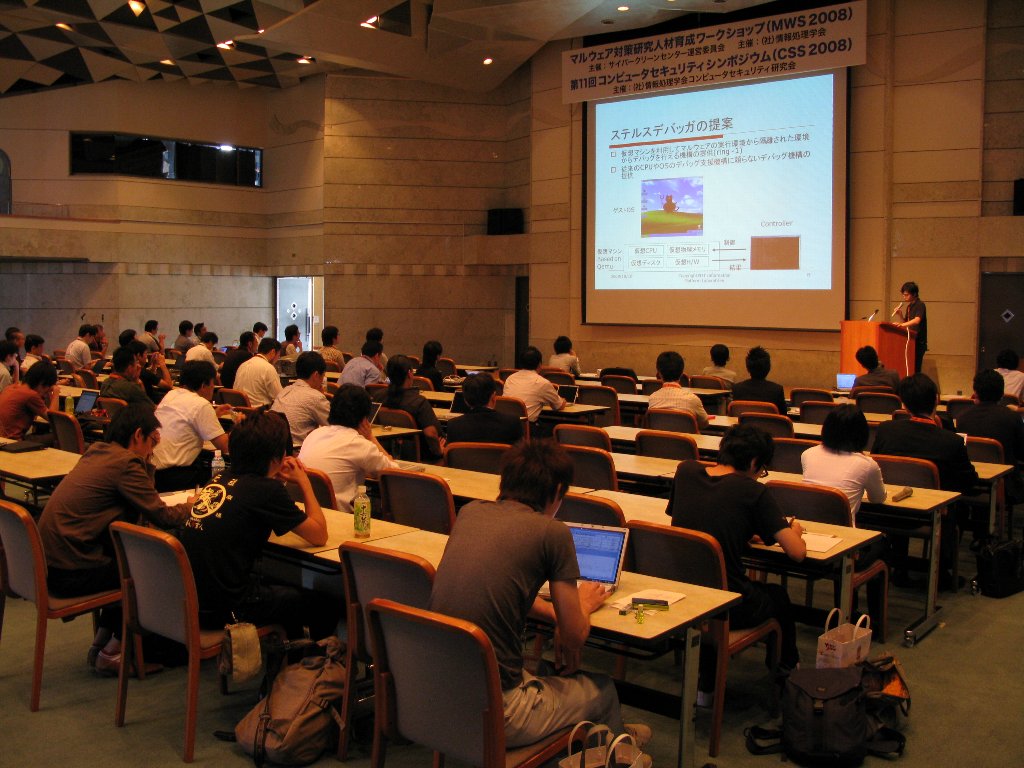
1007: Analyzing Malware with Stealth Debugger
Yuhei KAWAKOYA (NTT Information Sharing Platform Laboratories), Makoto IWAMURA (NTT Information Sharing Platform Laboratories) and Mitsutaka ITOH (NTT Information Sharing Platform Laboratories)[Abstract] In this papar,we introduce Stealth Debugger, an effective approach that stealthily debug malware that has anti-debug tricks. Stealth Debugger monitors programs running on guest OS from safe position, outside of OS and analyzes these programs by controlling virtual hardwares of the virtual machine monitor. Debugging functions of Stealth Debugger are totally independent from general OS and CPU debugging support. Therefore, we continue with analyzing malware without being detected by various malware debug detection techniques. In addtion, Stealth Debugger has signature breakpoint that capture characterictic instruction’s execution of programs running on guest OS. The signature breakpoint is adopted for unpacking malware by capturing the moment of jumping to original entrypoint. To demonstrate its effectiveness, we implemente that system and evaluate it with CCC DATAset 2008 malware.
[Manuscript in PDF(Japanese)]
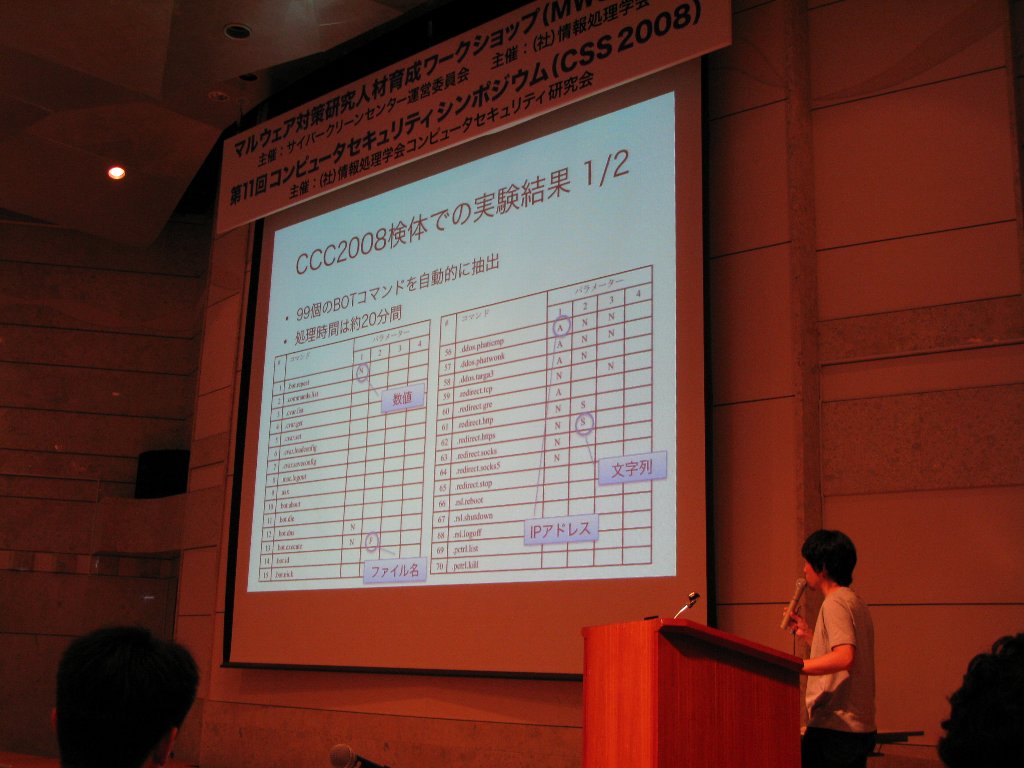
1013: Extracting BOT commands automatically by dynamic analysis
Yuji HOSHIZAWA (SecureBrain Corporation), Koichiro OKADA (SecureBrain Corporation) and Tsuyoshi TACHIKAWA (SecureBrain Corporation)[Abstract] In this research, we monitor and control the string manipulation functions of the Win32 API, and suggest a way of obtaining commands of target BOT. In the study of anti-BOT, it is important to know not only the behavior of BOT when infecting, but how it runs after infection by the commands from herder. Grasping all behavior of BOT including operation after commands reception is possible by static analysis, but getting all information in a short time is difficult. Also, it requires many analysis engineers to analyze and process the enormous amount of BOT. The system suggested in this paper solves these problems and enables us to get BOT commands quickly and automatically. In the early experiments, we confirmed the system extracts the commands and sends them to BOT automatically, and analyzes the behavior of BOT after the reception of each BOT command.
[Manuscript in PDF(Japanese)]
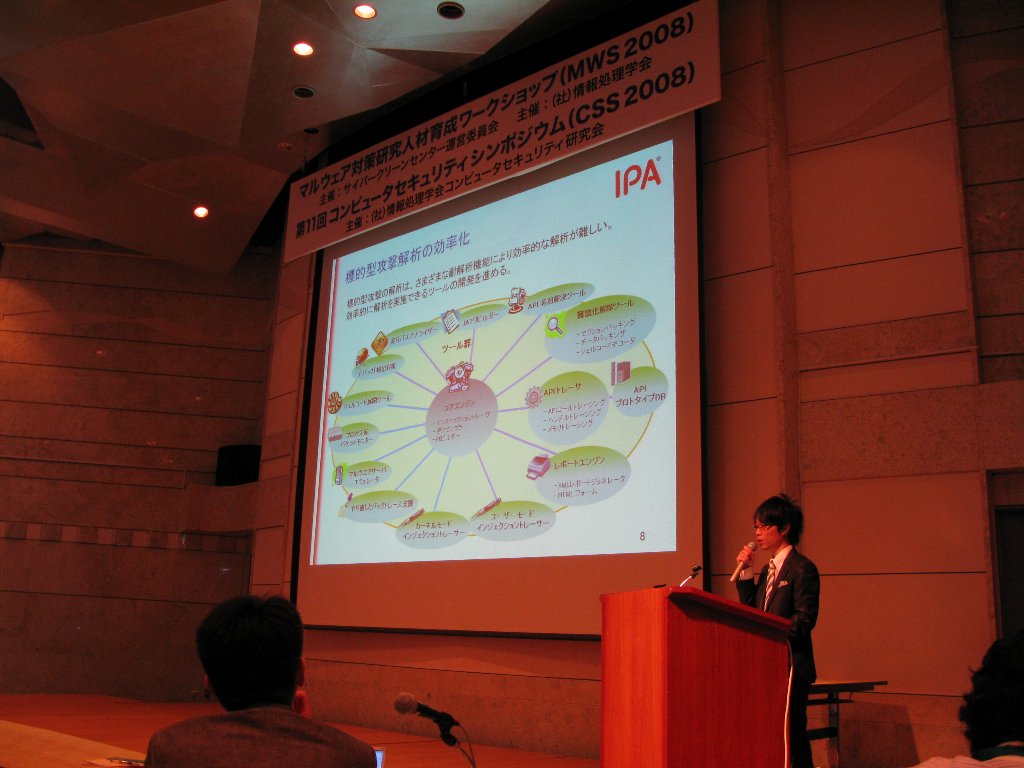
1024: An analysis tool for targeted attacks using security vulnerabilities
Yuji UKAI (Information Technology Promotion Agency, Japan), Hideaki KOBAYASHI (Information Technology Promotion Agency, Japan) and Manabu NAKANO (Information Technology Promotion Agency, Japan)[Abstract] Organizations are increasingly becoming the target of attacks following customized attack models. However in recent years attacks exploiting security flaws are increasing and anti-analysis techniques are widely implemented in malware thus making a quick and efficient analysis very difficult. Since performing effective steps to cope with attacks requires a detailed analysis of the code, we face a huge demand for techniques that allow quick and efficient coverage. This paper describes the exemplary implementation of techniques that automatically detect and cope with anti-analysis routines seen in recent years. Furthermore, it is an introduction to our implementation of these techniques - the "Customized Attack Analysis Tool". Our intention is to provide a tool to aid the quick and reliable analysis of anti-analysis techniques.
[Manuscript in PDF(Japanese)]
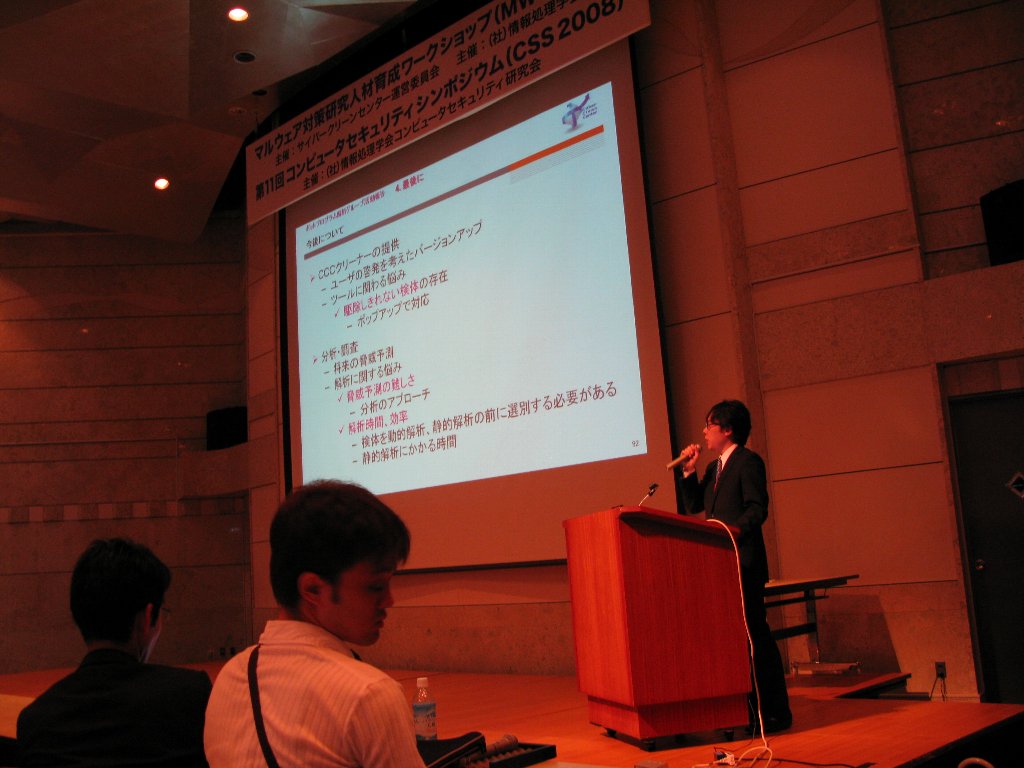
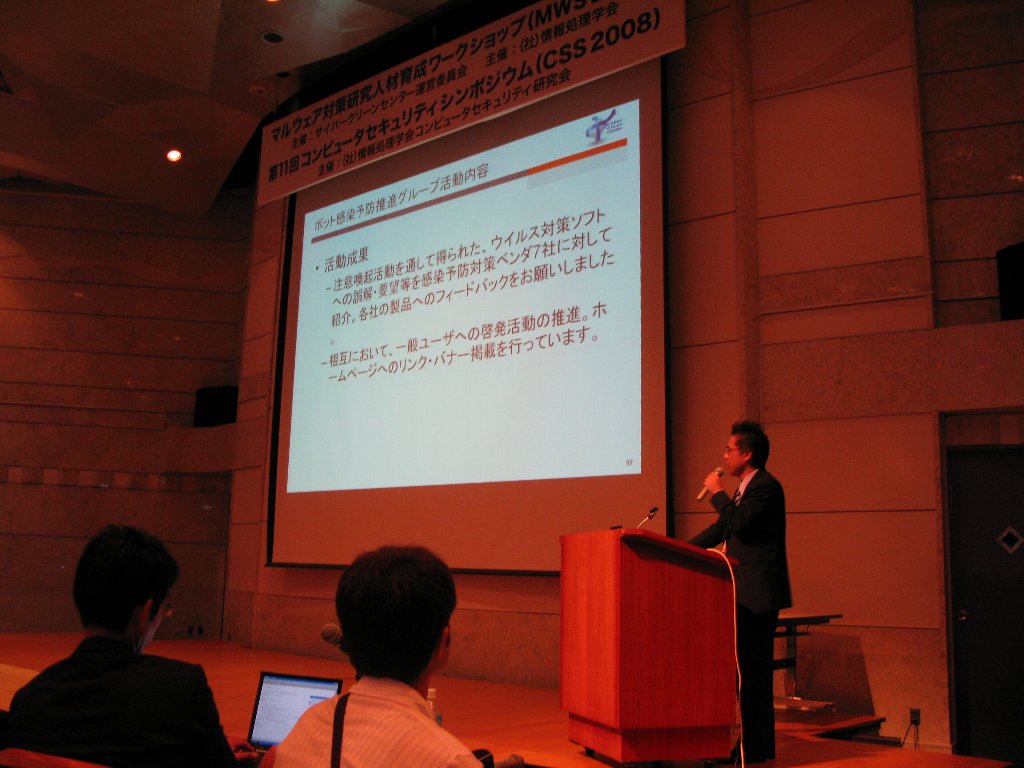
Session M7: CCC Activities Chair: Fumihiko Kosaka (JPCERT Coordination Center) 10:55 - 12:35
What is Cyber Clean Center (CCC) ? and Activities of CCC
Satoru NORITAKE (Telecom-ISAC Japan)Activities of the BOT program analysis group in CCC
You NAKATSURU (JPCERT Coordination Center)Activities of the BOT infection prevention promotion group in CCC
Tomomitsu MOCHIZUKI (Information Technology Promotion Agency, Japan)The trend of the BOTs activities
Toshiaki SUDOH (NTT,Communicatons Corporation)Session M8: Panel Discussion 2 Coordinator: Koichi ARIMURA (Telecom-ISAC Japan) 13:35 - 14:55
Best Student Paper Award
1005: Analysis of Malware Activities Based on Download Hosts
Hiroki ISHII (Okayama University)

Best Paper Award
1011: Visualization of Chain Infection and Guess of Sample Classification by Time Series Analysis
Takahiro MATSUKI (Little eArth Corporation Co., Ltd.)

Closing
Nov. 13, 2008
Published: 14:53 2008/10/13
Last Update: 7:15 2008/11/20
-
Copyright 2008 The CCC, Cyber Clean Center
& The IPSJ, Information Processing Society of Japan, All rights reserved.