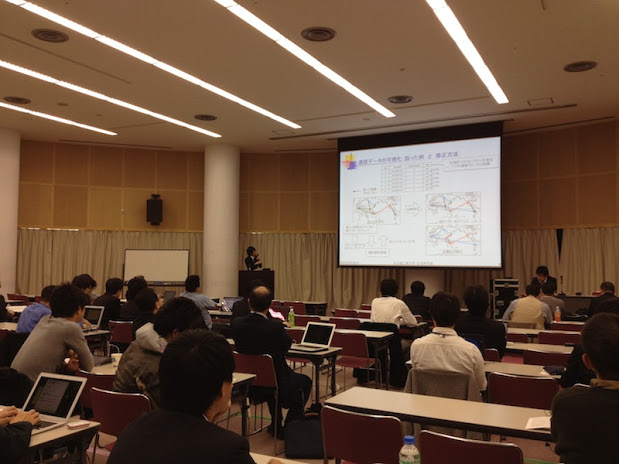
MWS 2012 - anti Malware engineering WorkShop 2012
October 30th - November 1st, 2012KUNIBIKI MESSE; Shimane Prefectual Convention Center, Shimane, Japan
Photo story of MWS 2012, Manuscripts and Slides
These manuscripts have been published without reviewing and editing as received from the authors: posting the manuscript to MWS 2012 does not prevent future submissions to any journals or conferences with proceedings.Awared Ceremony
1A1: MWS(Static Analysis) - Chair: Takashi Manabe
|
1A1-1: Tracing Malicious Code with Taint Propagation Yuhei Kawakoyay, Eitaro Shiojiy, Makoto Iwamuray and Takeo Hariu (NTT Secure Platform Laboratories) Dynamic malware analysis environments commonly distinguish their target code from benign code based on its process ID or thread ID. However, the distinction based on these IDs does not correctly handle? malware which has anti-analysis functions. To solve this problem, we propose an approach for identifying the to-be-analyzed code based on taint tags. To prove the effectiveness of our proposal, we have conducted experiments with a set of test code which behaves like malware and also with CCC Dataset2012. The results of these experiments indicated that our approach is effective against various anti-analysis functions, and that it is applicable to real malware. Our proposal will allow existing malware analysis environments and antimalware research to be more precise and effective. [ Manuscript (PDF) | Slide (PDF) ] |

|
|
1A1-2: Function Estimation Method for Malwares based on part of Binary Code Ryo Okubo, Masakatu Morii(Kobe University), Ryoichi Isawa, Daisuke Inoue and Koji Nakao(National Institute of Information and Communications Technology) Because malware analysis using similarities between malwares needs to make a lot of comparison, calculation amount is an important factor. Existing methods use LCS(Longest Common Strings) or n-gram to calculate similarity. The calculation amount of them is O(m×n). This calculation amount is not appropriate for making a lot of comparison. We propose a fast method for calculating similarity between malwares. We focus on distribution of byte code. To calculate a similarity between the two of malwares, we apply Zero-mean Normalized Cross-Correlation. Once we get the distribution of byte code, the calculation amount is O(1). Because this method does not influenced by file size, we can calculate similarity at short times in any case. Moreover we estimate function by adding point to each function according to similarity [ Manuscript (PDF) | Slide (PDF) ] |

|
|
1A1-3: Code Capture from Self-Modifying Malwares Noriaki Nakamuray, Masakatu Morii(Kobe University), Ryoichi Isawa, Daisuke Inoue and Koji Nakao(National Institute of Information and Communications Technology) Most malwares are packed or encrypted. In order to analyze such malwares, we have to unpack them and extract the original codes from them. There are many techniques of packing. It is difficult to extract original codes from malwares packed with multi-stage packers because their decryption algorithms is complicated. In this paper, we present our preliminary efforts toward generic binary unpacking against the three multi-stage packers, which are tElock, PESpin, and yoda’s Crypter. We find out that the thee packers has a common part of their algorithms. The packers finally reveal the original code of a malware to a specific section named‘.text section.’ That is, we set a break point in the section and can get the original codes of any malwares packed with the three packers. [ Manuscript (PDF) | Slide (PDF) ] |

|
1A2: MWS(Dynamic Analysis) - Chair: Katsunari Yoshioka
|
1A2-1: Malware Analysis Report 2012 using Malware Analyzer Alkanet Yuto Otsuki, Hiroaki Wakabayashi, Eiji Takimoto(Ritsumeikan University), Shoichi Saito(Nagoya Institute of Technology) and Koichi Mouri(Ritsumeikan University) Recently, malware has become a major security threat to computers. Responding to threats from malware requires malware analysis and understanding malware behavior. However, malware analyst cannot spend the time required to analyze each instance of malware because unique variants of malware emerge by the thousands every day. We are developing Alkanet, a malware analyzer that uses a virtual machine monitor based on BitVisor. We analyzed real malware samples using Alkanet. The samples are actual instances of malware recorded in CCC DATAset 2012. In this paper, we describe the analysis reports. [ Manuscript (PDF) | Slide (PDF) ] |

|
|
1A2-2: Design and Implementation of Malware Analysis using Network Emulator GINE Yasuaki Mitsueda, Kunio Goto and Hiroyuki Kawano(Nanzan University) Dynamic Analysis is effective for Malware. Although most malwares try to connect to the internet, Malware sample should be executed in disconnected the internet environment. For malware, not connecting the internet, malwares do not trigger their malicious behaviors. In this paper, we present design and implementation of malware traffic analysis using virtual network. We provide some fake services such as HTTP, IRC, DNS,SMTP and FTP in the virtual network. We analyze malware’s traffic. [ Manuscript (PDF) ] |

|
|
1A2-3: Malware Detection by Signature Matching in a Hypervisor Yoshihiro Oyama and Yudai Kawasaki(The University of Electro-Communications) We report the result of experiments in which we detected malware in the MWS 2012 malware dataset by using BVMD, a hypervisor that provides a malware detection mechanism. BVMD is implemented by extending a parapass-through hypervisor BitVisor. BVMD applies signature matching against data blocks that are transmitted between the guest OS and devices such as hard disks. [ Manuscript (PDF) ] |

|
2A1: MWS(Drive-by Download Analysis) - Chair: Takahiro Matsuki
|
2A1-1: A Malware Analysis Support System Combining Visualization and Dynamic Analysis Takayuki Yoshinori, Takuya Ban, Hitoshi Miyazaki, Takuya Matsui, Ryo Sato, Ryosuke Okazaki, Akihito Shinoda(Nagoya Institute of Technology), Masanori Hirotomo(Saga University), Masami Mohri(Gifu University), Masaki Kamizono(SecureBrain Corp.) and Yoshiaki Shiraishi(Nagoya Institute of Technology) Recently, the Drive-by-Download (DBD) attack increases threats which make users lead to the web sites distributing malwares. As countermeasure for this attack, we detect malicious web sites from the traffic data collected by crawling the web sites by client honeypots. However, it is infeasible to analyze each malicious code in huge traffic data. In this paper, we propose a system for supporting the analysis of the DBD attacks. The proposed system consists of two novel subsystems. The first subsystem is an interface which visualizes the traffic to focus on the attack flow. The second one is an analysis environment which automates dynamic analysis of the focused malicious codes. [ Slide (PDF) ] |
|
|
2A1-2: Classification of Hostile Javascript based on Encoding Abstract Syntax Tree Takuma Johnishi(Kobe University), Masaki Kamizonoz, Masata Nishida(Securebrain Corporation) and Masakatu Morii(Kobe University) In the recent years, the number of malware written in obfuscated Javascript has been increasing. Abstract syntax tree(AST) is used as a measure of classifying these malware to counter these malware. In previous research, it is proposed to use an AST based on structural analysis of polymorphic Javascript. However, Classi cation of Javascript has not been performed in the research. In this paper, we propose a method which enable to classifying Javascript by further abstracting AST and by encoding AST. Furthermore experimental results with the malware samples provided by MWS DATAset show that our proposed method can exactly classify and summarize hostile Javascript that is obfuscated in a similar way [ Manuscript (PDF) | Slide (PDF) ] |

|
|
2A1-3: Feasibility study of Observable Expression for Cyber Attack Countermeasure Masato Terada, Kazuki Iwamoto, Motoi Endo, Nozomi Matsuzaka and Hideaki Kobayashi(Information-technology Promotion Agency) Malware activities are progressing and changing for long term and short term, especially for the aspects of the function and implementation. For these progressing and changing, we should track them and keep up-to-date and reviewing for our information system security. In this paper, firstly we will describe implementation transition of email worm. Secondly, we will introduce our tracking approach for the aspects of the functional and implementation changing of outbound traffic of malware. [ Manuscript (PDF) | Slide (PDF) ] |

|
2A2: MWS(Special Session) - Chair:Mitsuhiro Hatada
|
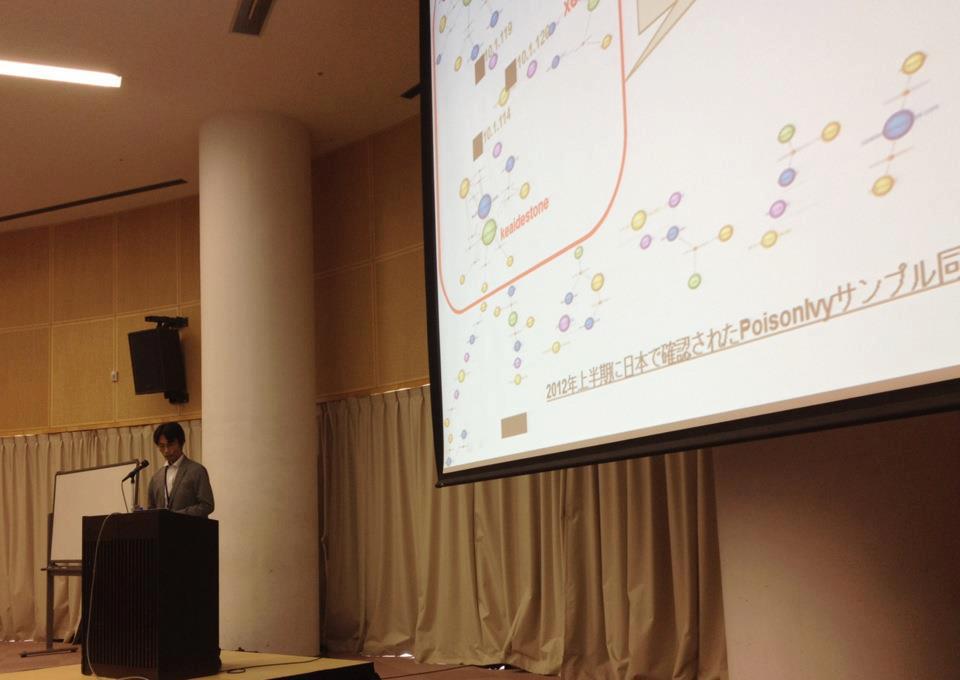
2A2-1: Bakuei Matsukawa - Trend Micro Inc. [ Slide (PDF) ] |
|
|
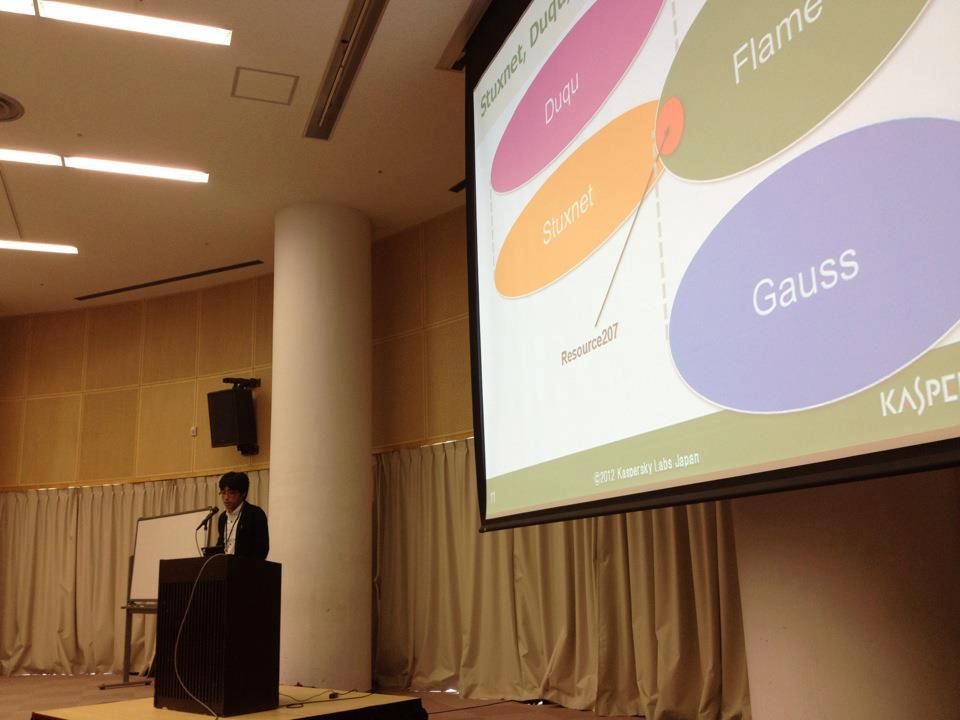
2A2-2: Norihiko Maeda - Kaspersky Labs Japan [ Slide (PDF) ] |
|
|
2A2-3: Ryoji Kanai - Fourteenforty Research Institute, Inc. |

|
|
2A2-4: Hiroshi Kawaguchi - LAC Co., Ltd. [ Slide (PDF) ] |

|
2A3: MWS(Special Session) - Chair:Mitsuhiro Hatada
|
2A3-1: Mamoru Saito - Internet Initiaive Japan Inc. [ Slide (PDF) ] |

|
|
2A3-2: Shinsuke Honjo - McAfee, Inc. |

|
|
2A3-3: Masakazu Takahashi - Microsoft Corporation [ Slide (PDF) ] |

|
2A4: MWS(Special Session) - Chair: Mitsuhiro Hatada
|
2A4-1: Ikuo Takahashi - BLT Legal Chambers [ Slide (PDF) ] |

|
|
2A4-2: Panel Discussion [Panelist] Bakuei Matsukawa - Trend Micro Inc. Norihiko Maeda - Kaspersky Labs Japan Shinsuke Honjo - McAfee, Inc. Ryoji Kanai - Fourteenforty Research Institute, Inc. Hiroshi Kawaguchi - LAC Co., Ltd. Mamoru Saito - Internet Initiaive Japan Inc. Masakazu Takahashi - Microsoft Corporation Ikuo Takahashi - BLT Legal Chambers [Moderator] Mitsuhiro Hatada - NTT Communications Corporation |

|
3A1: MWS(Traffic Analysis) - Chair: Daisuke Inoue
|
3A1-1: Development and Evaluation of the System to Detect C&C Server in Botnet Using Accumulated Data from CCC Nobuhiro Nakamura and Ryoichi Sasaki(Tokyo Denki University) Recently,the damage caused by the botnet has been increasing. There exists a problem that the other bot PCs can be produced, even if one bot PC could be specified and removed. Therefore, we proposed the Multi Stage Trace Back system on a proxy server program named Squid. We also evaluation second stage trace back method which consists of black list and Quantification methods No. 2 with CCCDataSet2009,2010,2011 and new parameters. This paper reports at first the system implemented for the 2nd Stage Trace Back, and then the results of functional experiment and performance experiment. |

|
|
3A1-2: Evaluating features of payload for malware detection Yusuke Otsuki, Masatsugu Ichino(The University of Electro-Communications), Kenji Kawamoto(Waseda University), Mitsuhiro Hatada(NTT Communications Corporation) and Hiroshi Yoshiura(The University of Electro-Communications) We evaluated features used in related works based on traffic data since effectiveness of using these features in malware detection is not evaluated sufficiently. In the evaluation, CCCDATAset and D3M2012 are used as anomaly traffic data infected with malware, and traffic data captured in some Intranet are used as normal traffic data. We evaluated the features by comparing the distances between normal/anomaly codebooks made by vector quantization and input data. In this paper, we show and discuss the evaluation results of payload features in each type of malware. [ Manuscript (PDF) ] |

|
|
3A1-3: A study of malware communication detection method that postulate the implemented to the IPS Sachio Ohnishi and Naoki Tsunematsu(MC Security Co., Ltd.) Because of the malware to perform software downloads and malicious attacks, such as remote control, damage report of unending information leakage. Also, anti-malware techniques have diversified accordingly. However, in order to take measures to malware that is increasing every day, there is a limit in the static defense techniques such as pattern matching. The results were analyzed CCC DATA set 2012 data set for research, we focus on the behavior of the communication that occurs of malware, in this paper, we propose a new method for dynamic defense IPS. [ Manuscript (PDF) | Slide (PDF) ] |

|
|
3A1-4: A Malware Detection Infrastructure System based on Stream Processing System Masahiro Ohke, Hideyuki Kawashima and Hiroyuki Kitagawa(University of Tsukuba) This paper proposes a malware detection infrastructure system based on stream processing system. The proposed system models packets as relational streams to solve the efficiency problem and generates results as relational streams to solve operation problem. We realize the proposed system based on SS* which we have developed, and we implement conventional methods. [ Manuscript (PDF) | Slide (PDF) ] |

|
MWS Cup
MWS Hands-on
|
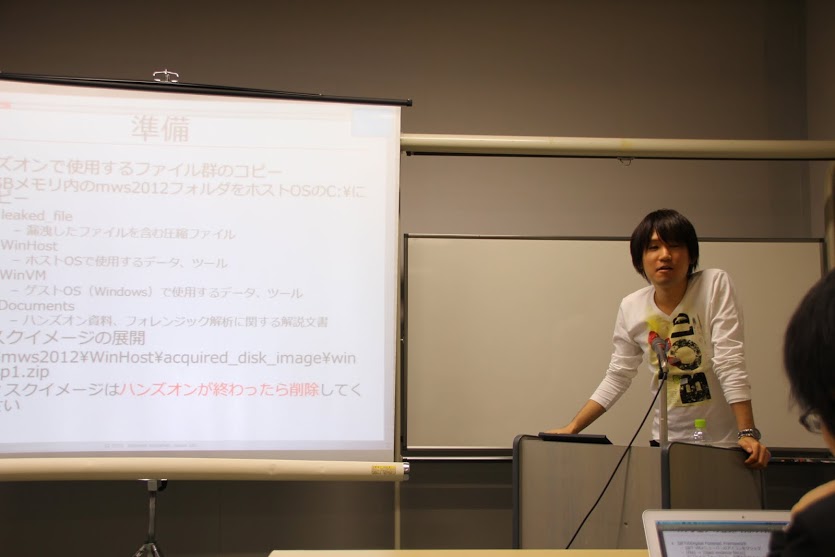
Static Analysis 101 (JPCERT/CC) |
|

|
|
Incident Response (IIJ) |
|
|