MWS 2016
- October 11 (Tue) - 13 (Thu), 2016
- Akita Castle Hotel, Akita, Japan
Photo story of MWS2016 / MWS Cup 2016
 |
Venue: Akita Castle Hotel |
 |
Award Ceremony
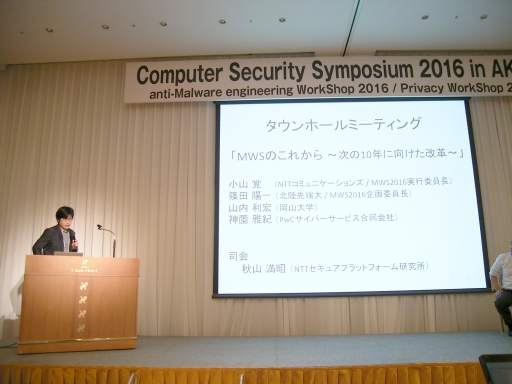
Special Session (Session 1B4, Chair: Mitsuaki Akiyama)
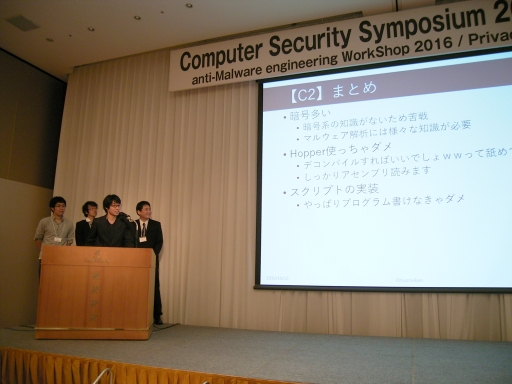
MWS Cup 2016
MWS 2016 Research Presentations
- Symbols
- * : presenter
- ** : student presenter
1B3: IoT/SECCON (session chair: Yoshihiro Oyama)
1B3-1: (Japanese version only)
1B3-2: IoT Malware Behavior Analysis and Classification Using Text Mining Algorithm
1B3-3: A Survey of Connection Form Between a Smart-Toy and a Smartphone (As of July 2016)
1B3-4: How to manage the online CTF (Capture the flag)
1F3: Malware and Encryption (session chair: Atsuo Inomata)
1F3-1: Encryption Processing of Ransomware
1F3-2: Locating Cryptographic Functions: an Evaluation
1F3-3: Proposal of identification to key generator using in encryption malware use
1F3-4: Identification of Cryptographic Functions in Malware Binaries ~implementation and evaluation~
2B1: Malware Detection / Classification (session chair: Toshihiro Yamauchi)
2B1-1: Analyze of Traffic Data and API Log for Estimating Object of Malware Infection Activity
2B1-2: Detectiong Malware Variants using Paragraph Vector
2B1-3: A Study of Characteristic of Malware Based on API Call Sequence and System Load Status Analysis
2B1-4: Malware process estimation method by multistage Deep Neural Networks based on process behavior
2F1: Network Wide Area Observation (session chair: Koichi Mouri)
2F1-1: (Japanese version only)
2F1-2: Estimation of Attackers' Intentions Based on Observation of Scanning Activities
2F1-3: Malware Originated HTTP Traffic Detection based on Request Interval and Response Body Size
2F1-4: The Effect of the Malware Infection on the Darknet Packets
2F2: Network Application Layer (session chair: Nobutaka Kawaguchi)
2F2-1: Implementation of a RAT Detection System using HTTP-Based Communication Behavior
2F2-2: Efficiency Improvement of Traffic Log Analysis of Multi-Environment Analysis for Malicious Websites
2F2-3: Effectiveness of Malicious Email Detection based on Double Bounce Emails
2F2-4: The proposal of new email system based on S/MIME concept for protecting the email between organizations from the targeted-email-attack
2B3: Malware Analysis Techniques (I) (session chair: Yosuke Hachimoto)
2B3-1: A preliminary study of dynamic analysis systems for Linux malware using TOMOYO Linux
2B3-2: Proposal of static analysis assistance method utilizing the dynamic analysis log
2B3-3: Analysis of Trends in Anti-virtualization Operations by Malware
2B3-4: (Japanese version only)
2F3: Network Malicious Communication (session chair: Yasuyuki Tanaka)
2F3-1: A Method for detecting C & C server using unobserved information by attackers
2F3-2: Detecting malware-infected hosts based on the variability of HTTP header fields
2F3-3: Log Detection of Malware-infected Host Communications with Data Compression Algorithm
2F3-4: Finding New Malware Samples with the Network Behavior Analysis
2B4: Malware Analysis Techniques (II) (session chair: Junichi Murakami)
2B4-1: Malware for Protocol Misidentification by utilizing Format-Transforming Encryption
2B4-2: An Unpacking Method based on Instruction-trace Similarity
2B4-3: (Japanese version only)
2B4-4: BinGrep: Proposing the efficient static analysis method by searching for the function comparing control flow graphs
2F4: Network Observation Technology (session chair: Daiki Chiba)
2F4-1: Estimation of The Number of Attack Sources for Novel Type Distributed SSH Login Bruteforce STBF
2F4-2: Host Independent and Distributed Detection system of the Network Attack by Using OpenFlow
2F4-3: SSH honeypot based on Linux container technology
2F4-4: A feature analysis of the IP address classes for detection of unknown malicious Web sites
3B1: Web Security and Machine Learning (session chair: Ryoichi Isawa)
3B1-1: Detecting Fraudulent Behavior Using Recurrent Neural Networks
3B1-2: (Japanese version only)
3B1-3: Development and evaluation of Analytical Support Application for Drive-by Download Attacks
3B1-4: Detecting Malicious Access based on Co-occurrence among Multiple Websites
3F1: Malware Data / Analisys (session chair: Yusuke Takahashi)
3F1-1: Overview of Research Data Set "Behavior Observable System 2016"
3F1-2: Time Series Analysis of Malware using Large-Scale Live Network Data
3F1-3: Classifying Malicious Documents based on the Nature of Cyber-Attack
3F1-4: A Path Tracing Method for Classifying Malicious PDF Files
3B2: Web Attack Analysis (session chair: Takahiro Kasama)
3B2-1: AETP: A Host based Intrusion Detection Method for Identifying Effective Web Attacks
3B2-2: Js-Walker - Analyzing Anti-analysis JavaScript framework for analysts with JavaScript API hooking
3B2-3: A Study for WAF signature generation for exploit
3B2-4: Continuous Evaluation of Drive-by Download Detection Method and A Study on Exploit Kits
3F2: Attack Detection / Classification (session chair: Ayumu Kubota)
3F2-1: Hybrid Anomaly Detection System with Random Forests and K-Means
3F2-2: Analysis of Malicious Access Logs Using the Session Graph
3F2-3: Investigation of Long-term Attacker Host's Behaviour
3F2-4: Towards Automatically Detecting Promotional Attacks in Mobile App Store
3B3: Web Tracking (session chair: Yoshinori Takesako)
3B3-1: An Implementation of Web Tracking Detection System and An Investigation of Third-party Tracking Sites
3B3-2: Browser Fingerprinting in Smartphone
3B3-3: Proposal and Implementation of Countermeasure against Event Tracking on Web
3B3-4: Web Tracking of Private Browsing with Browser Fingerprinting
3F3: Amp Attack Countermeasure (session chair: Takeshi Okamoto)
3F3-1: Quick response activity against DRDoS attacks utilizing AmpPot
3F3-2: (Japanese version only)
3F3-3: Defense against DRDoS Attacks by OpenFlow Switches
3B4: Malicious Website Analysis (session chair: Eitaro Shioji)
3B4-1: Analysis of Malicious Web Site using Various Environment
3B4-2: A Malicious Web Site Detection Technique using Link Structure
3B4-3: Implementation and Evaluation of Phishing Site Detection Method Using Image Local Features
3B4-4: Proposal of malignant Website discovery system for security incident analysis support
3F4: Attack and Defense (session chair: Masayuki Okada)
3F4-1: (Japanese version only)
3F4-2: Feasibility Study of Inter-Organizational Information Sharing for Cyber Security Countermeasure
3F4-3: Evaluation of Security Appliance against Persistent Attackers who has Prior Knowledge of Target Organization
3F4-4: Simulation of Coevolution on Attack and Defense in Cyberspace
Published: 2016/10/31
Last Update: 2016/11/24
Copyright 2016 The IPSJ, Information Processing Society of Japan,
All rights reserved.
Published: 2016/10/31
Last Update: 2016/11/24
Copyright 2016 The IPSJ, Information Processing Society of Japan,
All rights reserved.